How to Clean Up the Mess in Your Permissions Structure
Using Netwrix Access Analyzer
As IT environments grow and evolve, permission structures often become tangled, making it difficult to confirm that only authorized users can access or modify sensitive data.
Left unchecked, excessive permissions increase your attack surface and elevate compliance risks.
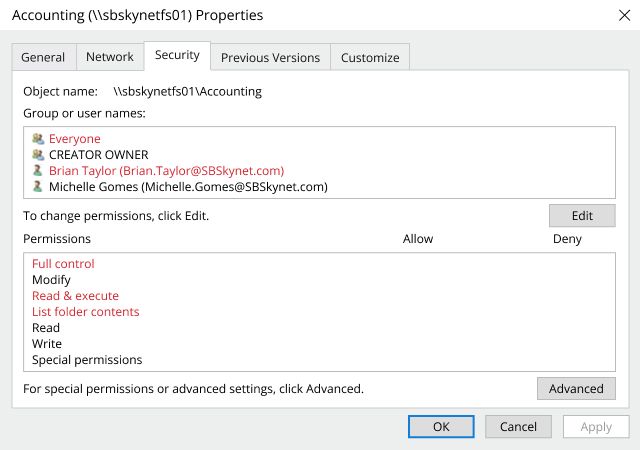
Common challenges in complex permissions structures include:
- Open (“Everyone”) access to sensitive data
- Users with unnecessary elevated privileges
- Overlapping permissions, such as both “Full Control” and “Read” rights
- Inconsistent naming conventions that obscure true access levels
Regain control of your permissions to reduce risk and strengthen security
Netwrix Access Analyzer gives you visibility into who has access to what across your file systems. It automatically detects excessive, redundant, or risky permissions and helps you enforce the principle of least privilege — while simplifying compliance reporting and audits.
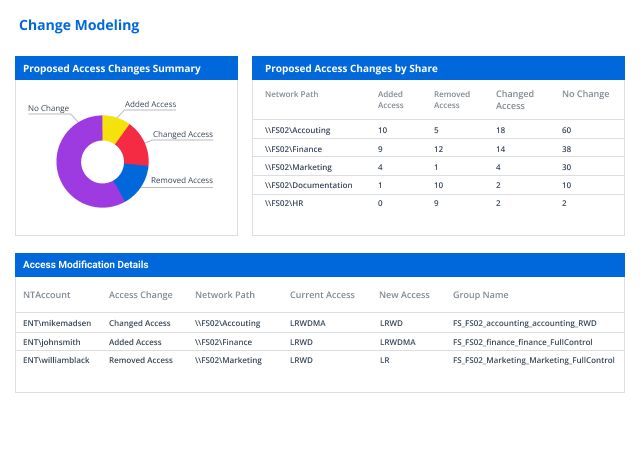
To get started, open the Access Analyzer Published Reports web client ⇒ Go to the File System tile in the Solutions set ⇒ and open the Change Modeling report.
The report provides a visual summary of proposed access changes and key insights, including:
- Proposed Access Changes by Share: A clear breakdown of recommended modifications for each file share to align with least-privilege principles.
- Access Modification Details: A granular view of affected users, groups, and permissions to understand what’s changing and why.
Automate permissions changes and maintain visibility with confidence
Netwrix Access Analyzer doesn’t just show you where the problems are — it enables you to fix them. Use the Action Module to automatically apply approved access changes and continuously monitor for new deviations. Every modification is tracked and logged, providing full transparency, audit readiness, and long-term control over your data access.






