Torna a tutte le soluzioni
Raggiungere e mantenere la conformità
Implementa zero trust per la gestione dell'identità e la sicurezza dei dati
Vantaggi chiave di Netwrix per operazioni di M&A e dismissione
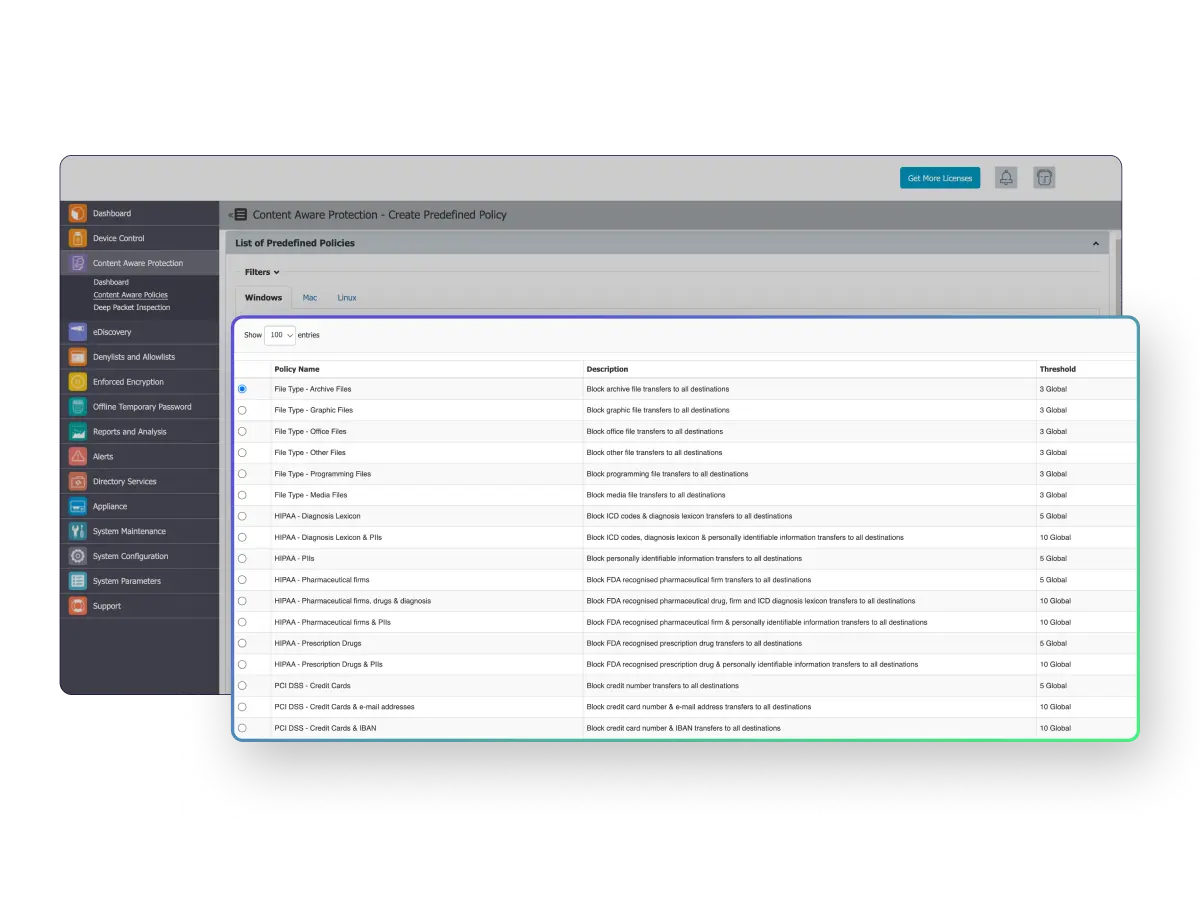
Come le soluzioni di Netwrix supportano i requisiti di conformità