Netwrix vs. Varonis: Broader visibility. Smarter control. Automated remediation.
Why Netwrix is the #1 Varonis alternative
Reduce data exposure, detect identity-driven threats in real time, govern identities, and remove standing admin rights — on your terms, on-prem or hybrid.
Varonis is ending support for on-prem. Netwrix continues to support how customers actually operate.
Why risk a forced migration?
With Varonis sunsetting all on-prem offerings by December 31, 2026, customers face a mandatory shift to SaaS whether they are ready or not. Netwrix provides continuity and choice — supporting on-prem, hybrid, and cloud deployments without disrupting operations.
- Stay in control of your data with flexible deployment options to address sovereignty, compliance, and security mandates.
- Avoid forced platform changes and preserve existing workflows with solutions that won’t require a disruptive migration.
- Modernize at your pace by adopting cloud capabilities when you choose — not because a vendor removes on-prem support.
Why settle for visibility alone?
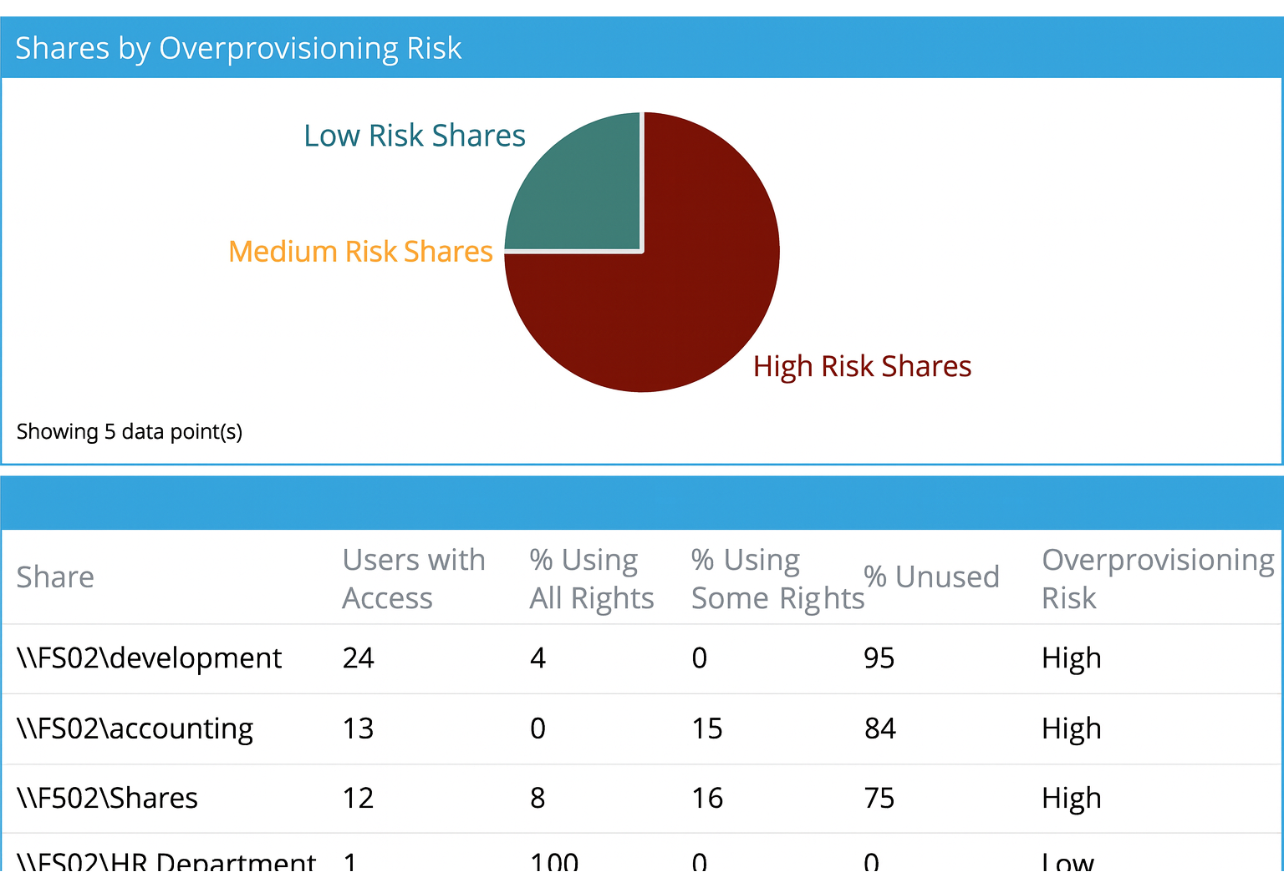
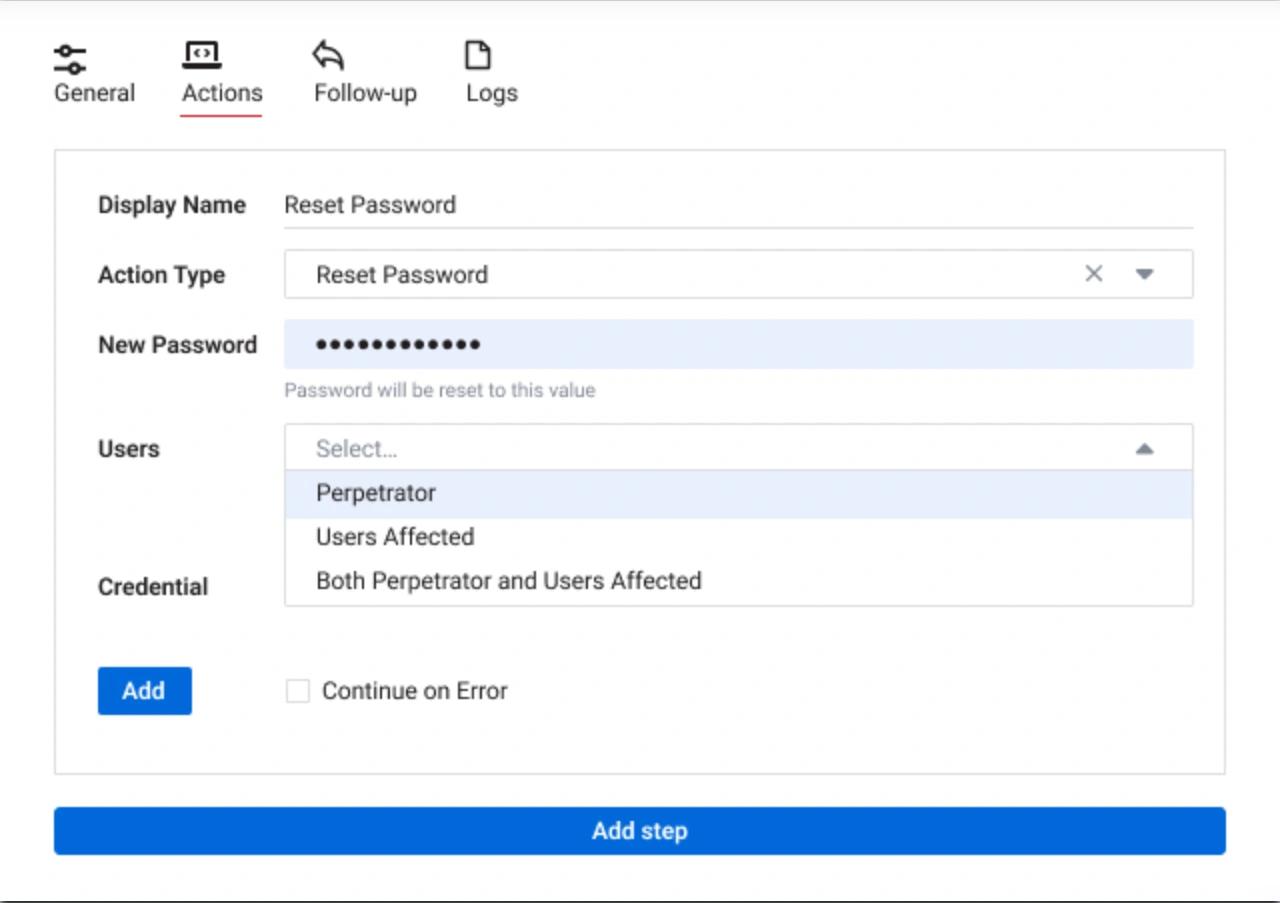
Where Varonis helps you see who has access to what, Netwrix empowers you to do something about it. Automatically detect, prioritize, and remediate data security risks — before they become breaches.
- Unify data and identity security across file systems, cloud repositories, databases, endpoints, and directories.
- Automatically fix risky permissions and enforce least privilege without scripting.
- Continuously monitor data activity to detect and stop insider threats or ransomware early.
Built for complex, hybrid environments
Unlike Varonis, Netwrix was built for hybrid enterprise ecosystems.
Gain deep visibility into sensitive data wherever it resides — from Windows and Linux servers to Microsoft 365, AWS, Azure, Google Cloud, databases, and endpoints.
- Data Discovery & Classification – AI-driven scanning, OCR, and customizable taxonomies with Microsoft Information Protection label support.
- Identity & Access Governance – Correlate entitlements from AD, Entra ID, and local accounts to expose hidden or shadow admins.
- Endpoint Data Loss Prevention – Block unauthorized transfers through email, browsers, USB, or cloud apps.
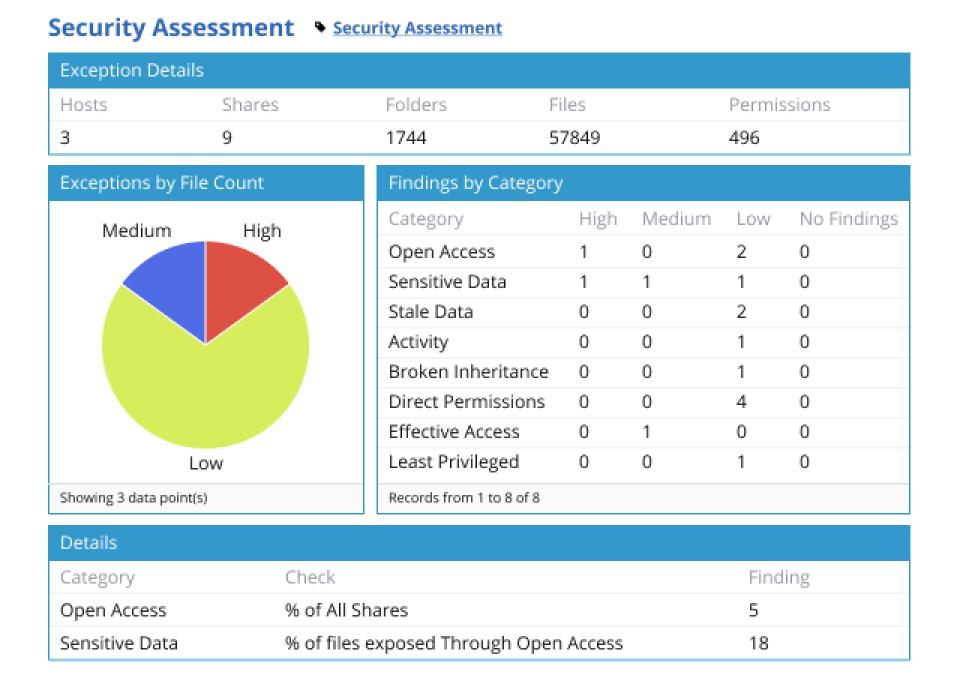
Compliance simplified
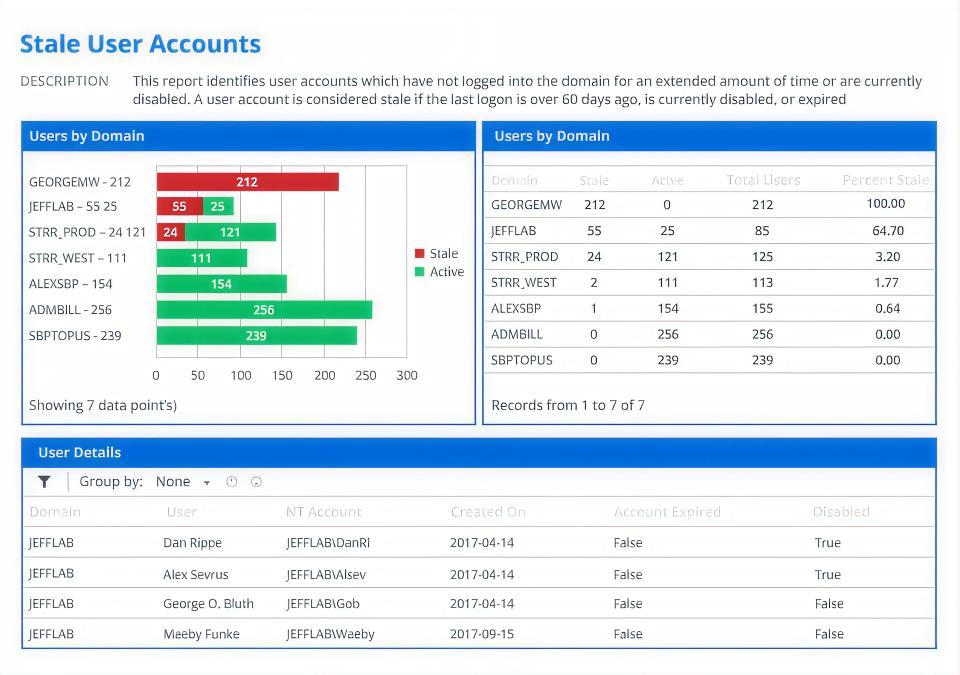
Approach compliance with confidence. Netwrix automates reporting and audit preparation for GDPR, HIPAA, PCI DSS, SOX, and more — saving hours of manual effort and audit stress.
- Pre-built frameworks and mapped reports.
- Automated audit-ready evidence generation.
- Quick response to data subject access requests (DSARs).
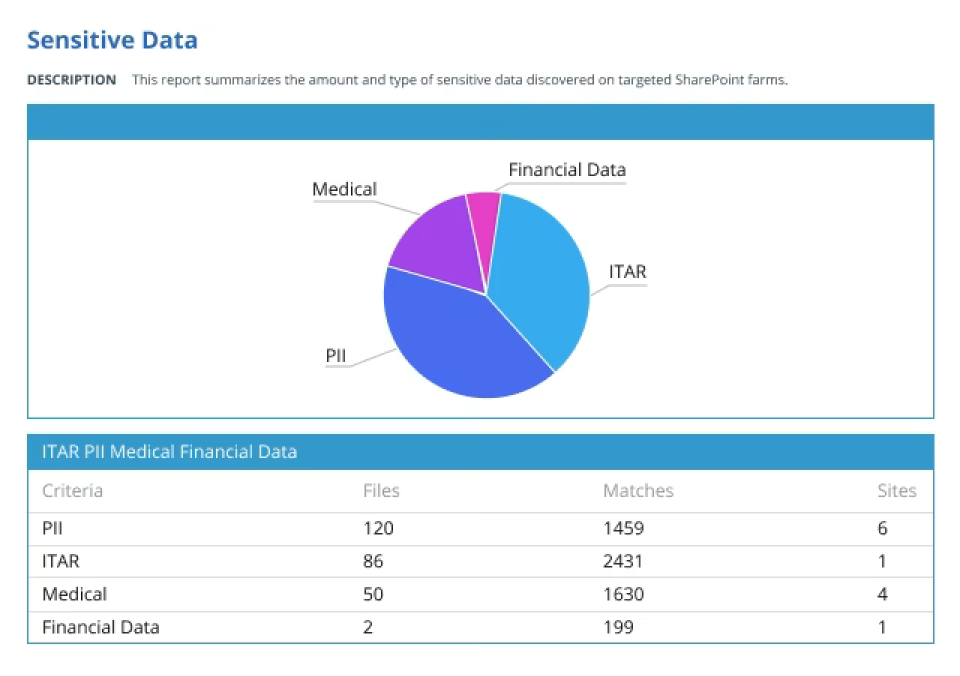
Identity-aware DSPM
Netwrix’s data security platform links data exposure directly to user identity and entitlement context, integrating Active Directory, Entra ID, and local accounts, to assess who has access, how, and why.
- Link data exposure to user identity: Netwrix ties instances of data exposure to the specific users and accounts responsible, revealing who has access, how they obtained it, and whether that access is appropriate.
- Unify identity and access context: By integrating with Active Directory, Microsoft Entra ID, and local accounts, Netwrix provides a single, correlated view of permissions across hybrid environments.
- Enable precise, risk-based decisions: Security and IT teams can prioritize remediation and enforce least privilege confidently, knowing exactly which identities pose the greatest risk to sensitive data.
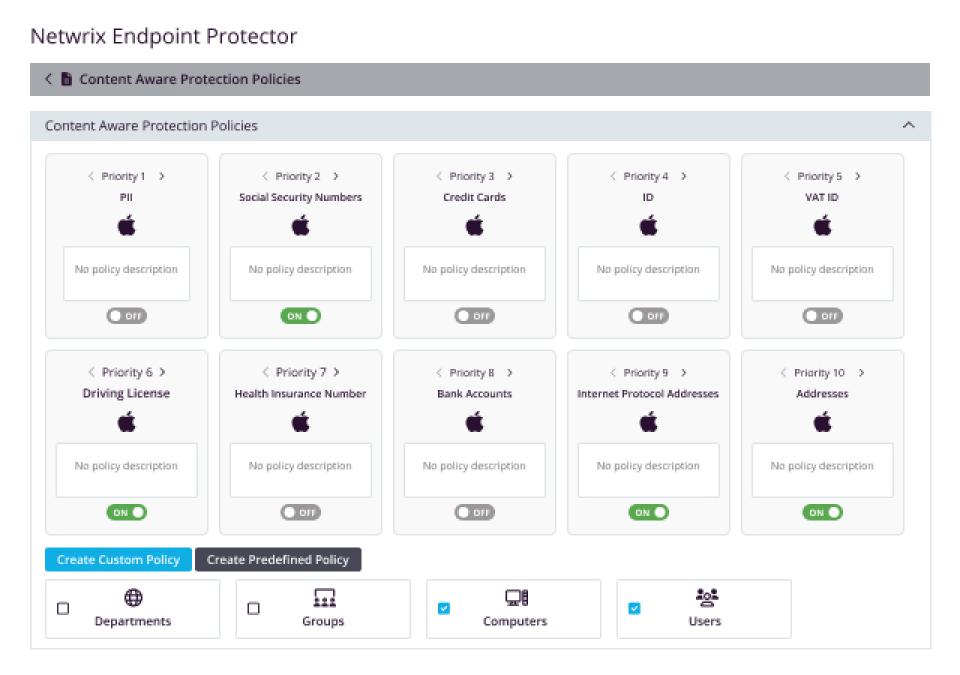
Active data protection at the endpoint
Netwrix’s endpoint protection solutiondelivers content-aware DLP across Windows, macOS, Linux, and GenAI tools, preventing data loss via devices, browsers, and cloud apps.
- Stop data leaks before they happen: Continuously monitor and block unauthorized transfers of sensitive data through USB devices, browsers, email, Copilot and other GenAI tools, and cloud applications.
- Protect every endpoint, everywhere: Enforce consistent data loss prevention policies across Windows, macOS, and Linux systems, even for remote or offline users.
- Detect sensitive content in motion: Use deep, content-aware inspection to identify regulated or confidential information and prevent it from leaving the organization.
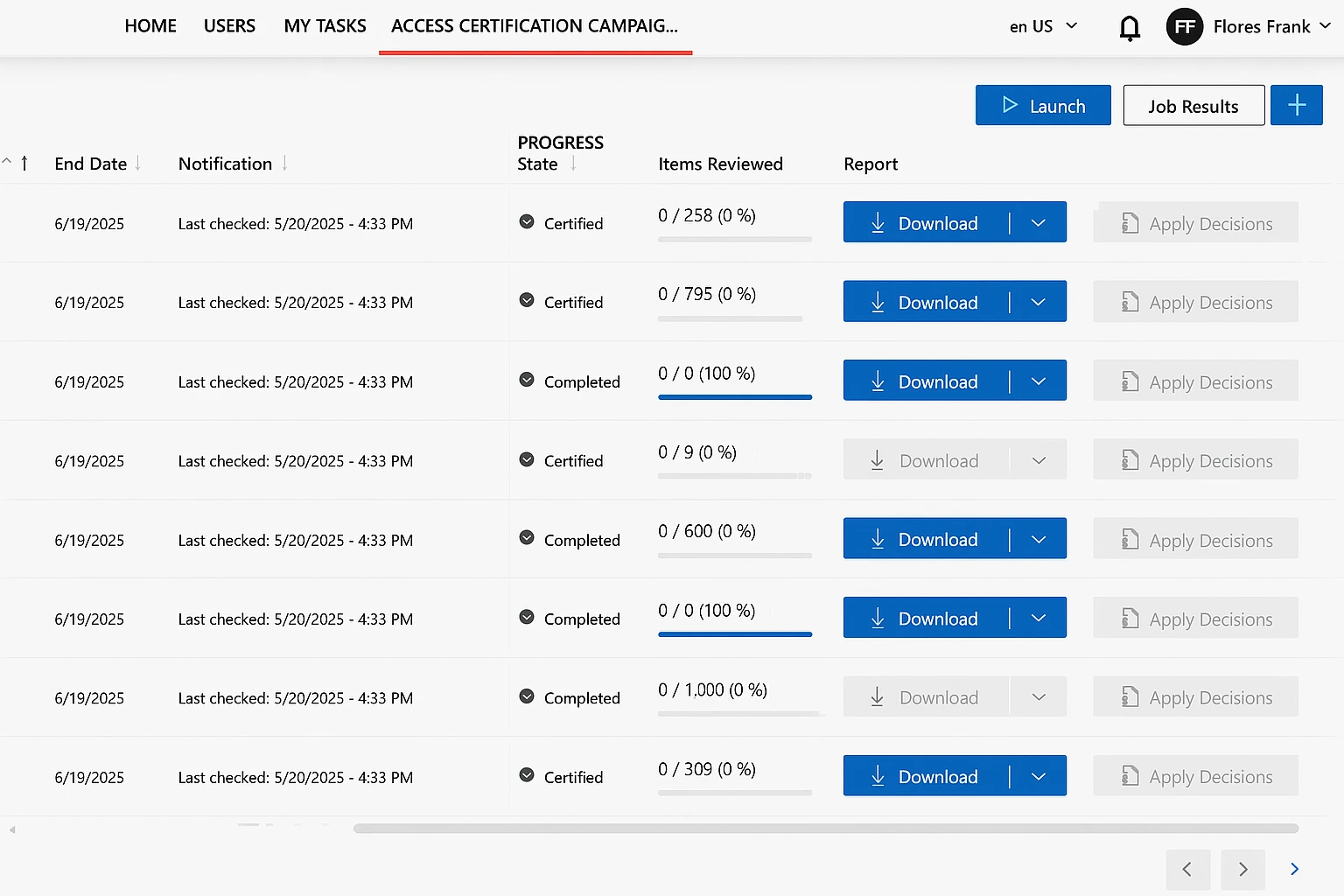
True identity governance meets data security
While Varonis focuses on visibility into file-level permissions, Netwrix delivers full Identity Governance and Administration (IGA) — automating user, role, and entitlement lifecycles across IT and business systems. It bridges identity compliance and data security, giving organizations unified control and accountability from onboarding to access recertification.
- End-to-end identity lifecycle automation: Manage joiner, mover, and leaver processes across hybrid environments with workflow-driven provisioning and deprovisioning.
- Comprehensive access governance: Empower managers and data owners to conduct periodic access reviews, enforce segregation of duties, and maintain continuous least-privilege access.
- Risk detection and policy enforcement — Continuously detect identity risks such as conflicting entitlements, segregation-of-duties violations, and dormant accounts. Apply policy-based controls to prevent privilege escalation before it leads to data exposure.
Varonis focuses on visibility. Netwrix delivers real control.
Secure what actually matters.
With Netwrix, you get end-to-end protection across data, identity, and endpoints, so you can prevent threats, not just monitor them.
Hosting
SaaS-first; on-prem estates face migration
On-prem and SaaS
Threat management
Alerting only
Alerting and blocking
Active Directory security
Reporting and alerting
Detecting and blocking
Privileged Access Management
No dedicated PAM
Full PAM capabilities
DLP / Endpoint Protection
No data exfiltration prevention
Prevents data exfiltration across dozens of egress points
Identity Governance and Administration
No IGA capabilities
Full IGA capabilities
Copilot security
Prompt monitoring
Monitoring and blocking of prompts
Compliance reporting
Limited
Pre-built, automated
Data discovery and classification
Varonis is blind to the location of your data
AI + contextual
Deployment
Cumbersome deployment, requires the installation of multiple agents
Easy and straightforward deployment
Licensing
Complex, volume-based
Transparent, modular
The Netwrix stack at a glance
Data Security Posture Management (DSPM)
Finds and protects sensitive data, prioritizes and roots out compliance risks, and shuts down risky behavior before it becomes a breach.
Identity Threat Detection & Response (ITDR)
Detects AD & file-system attack patterns with automated/guided response. Proactively prevents threats, detects and contains AD & file system attacks faster, and recovers quickly to keep businesses resilient.
Privileged Access Management (PAM)
Discovers local and admin accounts, enforces Zero Standing Privilege with Just-In-Time access, monitors and records sessions, and provides approvals & full audit trails.
Identity Management
Secures identities, streamlines processes, automates provisioning, enforces least privilege, and maintains continuous audit readiness.
Ready to see how Netwrix outperforms Varonis?
Request a personalized demo to explore how Netwrix secures your data and identities.
This page expresses the opinion of Netwrix and the information herein is subject to change. The non-Netwrix company names and products referenced on this page are not sponsors of Netwrix or otherwise affiliated with Netwrix. Their names, logos and other identifying marks are trademarks of and owned by each represented company and/or its affiliates.






