Shadow AI security
Prevent sensitive data leaks to AI tools across endpoints
Employees use AI tools without oversight, exposing sensitive data through prompts, uploads, shares, and clipboard actions that bypass traditional security controls.
Uncontrolled AI tool usage
Employees adopt public LLMs and copilots outside IT governance. Sensitive data is shared without visibility or approval, creating unmanaged exposure paths that security teams cannot monitor or control in real time.
Sensitive data exposed in prompts
Users paste intellectual property, credentials, and regulated data into AI tools. Up to 10% of prompts contain sensitive data, increasing the risk of leakage, reuse, and compliance violations .
Limited visibility into endpoint activity
Security teams lack insight into how data moves across endpoints, browsers, and apps. Without visibility into uploads, prompts, and transfers, unauthorized AI usage remains hidden until after exposure.
Inconsistent policy enforcement across endpoints
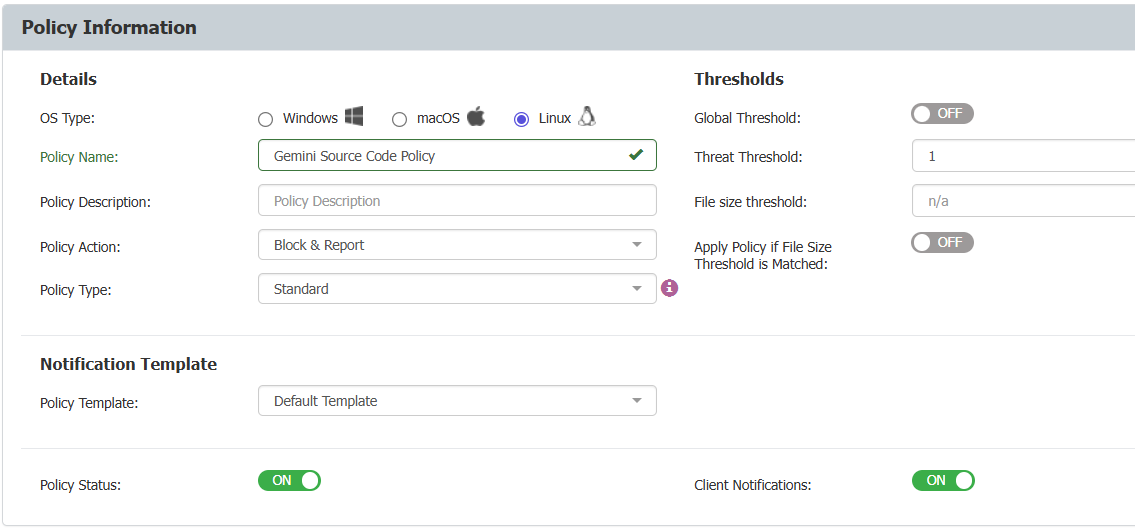
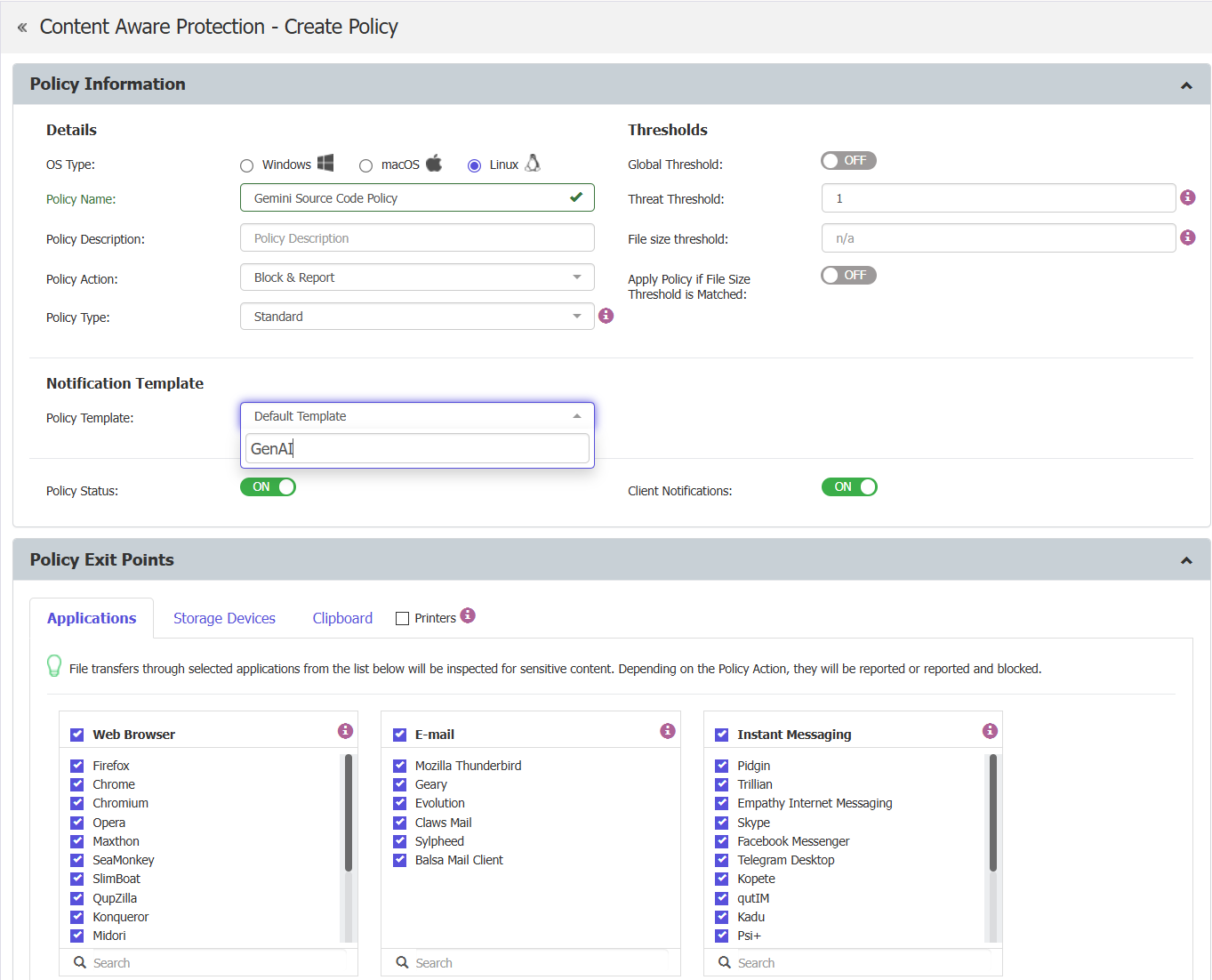
Hybrid work and mixed operating systems create enforcement gaps. Traditional tools cannot apply consistent policies across Windows, macOS, Linux, and offline devices, increasing data loss risk.
Prevent data loss to AI tools with real-time endpoint controls
Netwrix Endpoint Protector delivers real-time, content-aware data loss prevention across endpoints, applications, and AI tools. It inspects data in motion and at rest and enforces policies based on sensitivity, user identity, and destination risk. With consistent protection across operating systems and offline devices, organizations gain visibility and control over Shadow AI usage.
Block sensitive data in AI tools
Prevent users from entering sensitive data into AI prompts with context-aware policies that inspect content and block risky actions in real time.
Gain visibility into AI usage
Monitor how users interact with AI tools across browsers, apps, and endpoints. Detect shadow AI activity early with detailed logs and reporting.
Enforce policies without disrupting work
Apply granular controls based on user, data type, and application. Allow approved AI tools while blocking risky behavior to maintain productivity.
Protect data across all endpoints
Enforce consistent DLP policies across Windows, macOS, Linux, and offline devices to eliminate gaps in hybrid and remote environments.
Features that eliminate shadow AI