Volver a todas las soluciones
Seguridad de confianza cero
Implementar cero confianza para la gestión de identidad y la seguridad de datos
Beneficios clave de Netwrix para la implementación de zero-trust
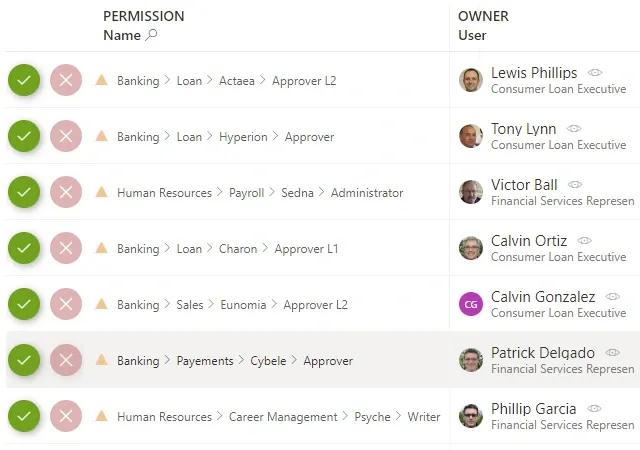
Cómo las soluciones de Netwrix habilitan un marco de confianza cero
Los principios de Zero Trust habilitados a través de las capacidades de Netwrix