AD CS Attack Prevention
Stop certificate-based identity attacks before they bypass your credentials, escalate privileges, and persist undetected.
AD CS is a growing and largely unmonitored identity attack surface. Attackers exploit certificate trust to bypass MFA, escalate privileges, and maintain persistent access, even after password resets or account disablement.
AD CS is an overlooked attack surface
Active Directory Certificate Services is widely deployed but rarely monitored, leaving organizations exposed to a growing class of identity attacks that bypass credentials, MFA, and traditional detection entirely.
Certificates outlast credential resets
Once issued, certificates remain valid even after password changes or account disablement. Attackers who obtain a certificate maintain persistent access that standard identity security controls cannot revoke.
Misconfigured templates enable privilege escalation
Insecure certificate template settings allow low-privileged users to enroll certificates for privileged accounts, enabling privilege escalation, lateral movement, and domain takeover through documented ESC techniques.
Limited visibility into certificate activity
Native Windows logging for AD CS is incomplete and rarely monitored in real time. Defenders lack visibility into who requested which certificate, which template was used, and whether SANs were manipulated.
Detect, block, and audit certificate-based attacks in real time
Netwrix delivers real-time visibility and blocking across the full AD CS lifecycle, from enrollment requests to certificate issuance and use. By intercepting suspicious certificate activity before it completes, Netwrix prevents attackers from exploiting certificate trust to bypass credentials, escalate privileges, and persist undetected across the environment.
Stop attacks before certificates are issued
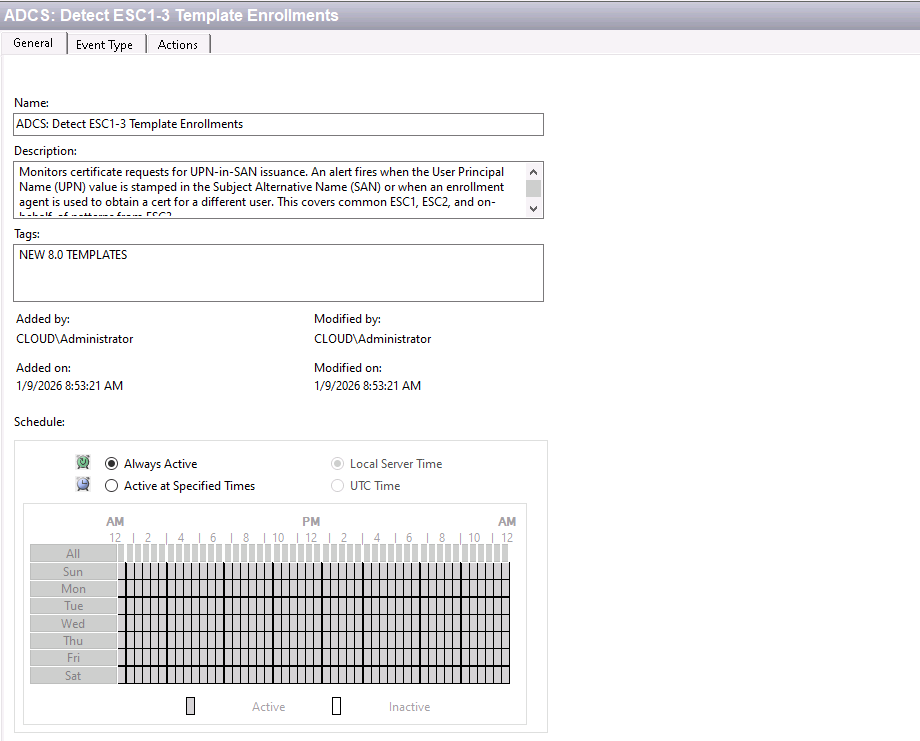
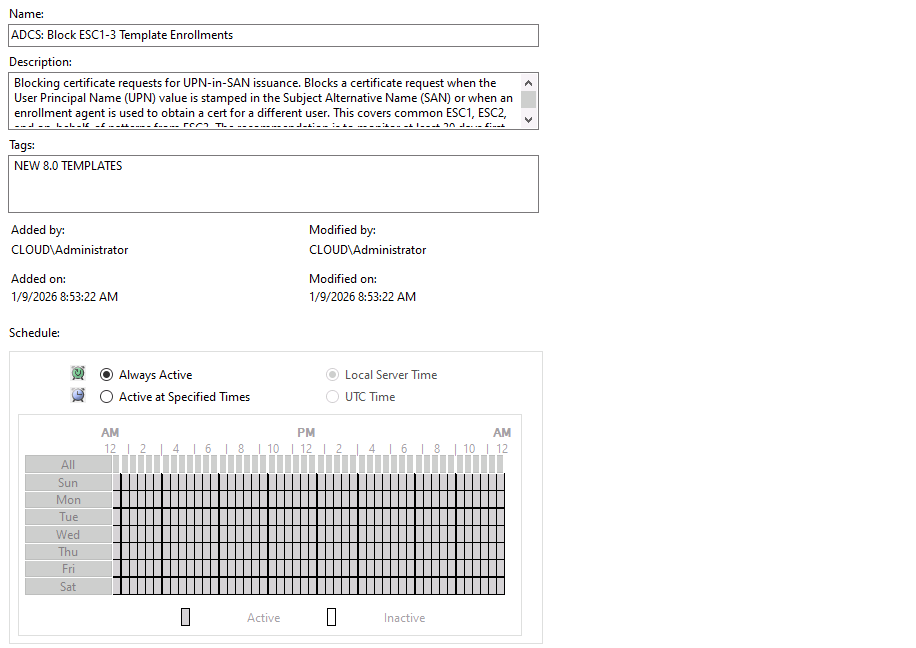
Intercept certificate enrollment requests at the CA before issuance, capturing full request context to detect and block abuse in real time, not after the fact.
Block the full ESC attack spectrum
Automatically deny requests matching documented ESC1–ESC4 attack patterns, before a certificate is ever issued.
Audit every template and CA change
Track every modification to certificate template ACLs, CA flags, enrollment agent settings, and issuance requirements to catch misconfigurations before attackers exploit them.
Track every certificate from request to logon
Correlate certificate issuance with authentication events to identify unauthorized certificate-based logons, weak account mappings, and missing SID extension scenarios.
Close the identity security coverage ga
Most identity security solutions stop at credentials. Netwrix extends identity threat detection to the certificate channel, covering the attack paths that traditional d tools miss.
Features that power AD CS threat detection and blocking