UEBA (User and Entity Behavior Analytics): complete guide to detection, use cases, and implementation
Apr 22, 2026
User and entity behavior analytics (UEBA) is a cybersecurity technology that uses machine learning and risk scoring to detect threats by analyzing user and entity behavior patterns. UEBA establishes behavioral baselines for users, devices, and applications, then identifies anomalies that may indicate insider threats, compromised accounts, or advanced attacks that traditional security tools miss.
What is UEBA?
User and entity behavior analytics (UEBA) is a cybersecurity technology designed to spot threats that may evade traditional security tools. It continuously analyzes how users and entities behave across an organization’s environment and flags activity that deviates from the norm.
UEBA uses artificial intelligence (AI), machine learning (ML), and risk scoring to establish a behavioral baseline for users and entities (such as endpoints, servers, applications, service accounts, and even IoT devices). When behavior suddenly changes, like a user accessing sensitive data at unusual hours or a server making unexpected outbound connections, UEBA raises the alarm before damage occurs.
UEBA emerged in response to a growing problem: not all threats look like attacks.
- Insider threats usually involve legitimate credentials, making them invisible to perimeter-based defenses.
- Advanced persistent threats (APTs) move slowly and quietly, blending into normal activity to avoid detection.
- Rule-based and signature-based tools struggle with unknown threats, alert fatigue, and false positives.
UEBA addresses these gaps by focusing on behavior, not just events. Instead of asking “Is this action on a blocklist?”, UEBA asks a more powerful question: “Does this behavior make sense for this user or entity right now?” By providing a context-aware view of activity across the organization, UEBA cybersecurity technology is an effective shield against today’s security threats.
UEBA vs. UBA: what’s the difference?
UBA is a subset of UEBA. While user behavior analytics (UBA) focuses solely on human users and their actions, UEBA analyzes behavior across:
- Human users, including employees, contractors, consultants, vendors, and privileged users
- Non-human entities such as servers, databases, applications, service accounts, and devices
This broadened scope aligns with modern environments where machines outnumber people, and compromised service accounts or misbehaving systems can be just as dangerous as malicious insiders.
Discover how to prevent identity-based attacks, reduce risk, and respond faster with Netwrix ITDR. Get a demo.
How UEBA works
UEBA works by continuously monitoring activity across an organization’s digital environment, including user, device, application, and network activity. It learns what “normal” looks like and identifies behavior that falls outside those patterns. Instead of analyzing isolated events, UEBA connects signals from multiple sources to build context, making it easier to detect subtle, high-risk activity.
Here is a detailed discussion on how UEBA works.
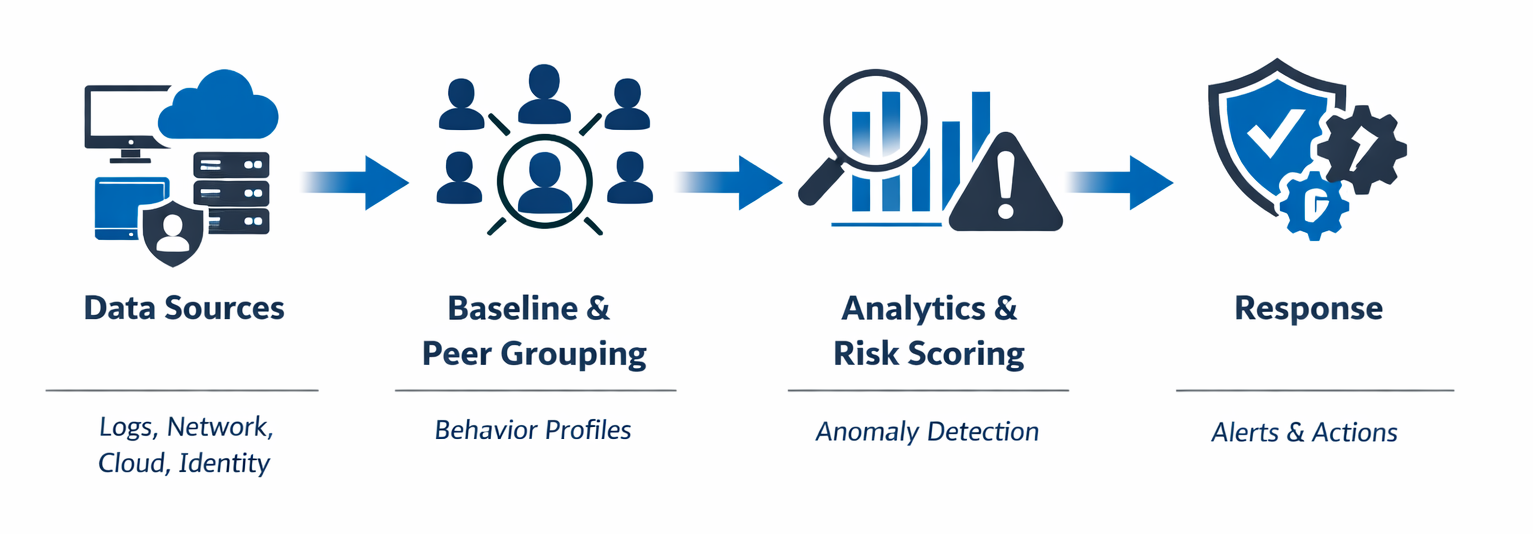
Data collection and sources
UEBA systems start by aggregating and correlating data from across the IT ecosystem. By pulling in activity from multiple sources, it creates a unified view of how users and entities interact with systems and data. Typical data sources include:
- Identity systems such as Active Directory for user authentication events
- IAM systems for access management logs
- VPN connections for remote access patterns
- Database access logs, file servers, web proxies, and application-specific logs
- Email and collaboration tools for communication behaviors
- Endpoint detection and response (EDR) solutions for device-level activities
- Cloud services and SaaS platforms
- Network traffic and existing SIEM data
This positions UEBA to spot patterns that would be invisible if each system analyzed events in isolation. This also ensures that suspicious activities are detected even when attackers attempt to blend malicious actions across multiple systems.
Establishing baselines and peer groups
Once data is collected, UEBA builds dynamic behavioral baselines for each user and entity. These baselines reflect normal behavior, such as login times, geographic locations, access patterns, application usage patterns, devices used, data transfer volumes, and typical workloads. These baselines evolve as behavior changes over time, such as someone taking on new responsibilities or shifting to different working hours.
UEBA also uses peer group analysis, where it compares behavior among users or entities with similar roles, access levels, or functions. For example, a marketing analyst accessing financial databases might be unusual compared to their marketing peers. Or a finance user accessing engineering systems may be normal in one role but suspicious in another. Peer grouping adds critical context, allowing UEBA to detect meaningful anomalies rather than harmless variations.
Analytics and anomaly detection
UEBA uses machine learning models that continuously analyze user and entity behaviors against established baselines and peer group norms. When behavior deviates significantly (such as unusual data access or abnormal login locations), UEBA assigns a risk score based on numerous factors, including:
- Severity of deviation from baseline
- Sensitivity of accessed resources
- Frequency of concurrent anomalies
- Historical context
- Threat intelligence correlation
A single minor deviation generates a low risk score, while multiple suspicious activities occurring in sequence trigger a high-priority alert.
Because UEBA focuses on behavior and risk rather than single events, it reduces false positives. Contextual analytics reduce alert noise by understanding the circumstances surrounding each event. For example, a login from an unusual location might trigger an alert, but if the user recently submitted a travel request and is working during business hours, the context suggests legitimate activity.
Alerting and response
When UEBA detects anomalies that exceed risk score thresholds, it generates alerts enriched with forensic context, including timelines, affected systems, the specific behavior that triggered the alert, relevant baseline comparisons, the calculated risk score, and suggested response actions. This allows security teams to quickly understand what happened and why it matters. Depending on the integration and configuration, UEBA can also trigger automated responses, such as:
- Temporarily locking or disabling accounts
- Enforcing step-up authentication
- Limiting access to sensitive resources
- Session termination for active connections
- Escalating incidents to security teams
In addition to real-time alerting and response, the system preserves detailed audit trails of user activities, historical behavioral patterns, investigation outcomes, and response actions taken. This supports long-term investigations, threat hunting, and compliance reporting.
UEBA use cases
UEBA is most effective when applied to real-world security challenges where traditional controls fall short. Advanced analytics provides visibility into subtle behavioral changes that indicate compromise or malicious intent.
Insider threats (malicious or negligent)
Insider threats are not always intentional. UEBA can identify both malicious insiders and well-meaning employees and privileged users who make risky mistakes. Examples include excessive access to sensitive files, unusual privilege escalation, and downloading data outside normal job functions. By understanding baseline behavior, UEBA can flag warning signs before a serious incident occurs.
Compromised accounts and brute-force attempts
Stolen credentials are one of the most common attack vectors. UEBA detects compromised accounts by identifying abnormal login patterns such as impossible travel, unusual access times, repeated authentication failures followed by success, and access from unfamiliar devices. The system also recognizes brute-force attack patterns across multiple accounts, even when individual failed login attempts fall below traditional thresholds. Even when credentials are valid, UEBA can spot behavior that does not match the user’s profile.
APT detection and lateral movement
Advanced persistent threats (APTs) are designed to evade perimeter defenses by moving slowly and deliberately through an environment. UEBA can uncover them by detecting lateral movement, privilege abuse, reconnaissance activities, and unusual access paths between systems. For example, a user account accessing servers it has never accessed before may indicate an attacker expanding their foothold.
Data exfiltration and DLP correlation
UEBA plays a critical role in detecting data exfiltration. It can correlate user behavior with data movement patterns to identify abnormal data access, large file transfers, unusual uploads, or printing sensitive documents outside normal patterns. By combining DLP alerts with behavioral context, security teams can distinguish between legitimate business activities and data theft.
IoT or server compromise visibility
Traditional security monitoring tends to overlook non-human entities. UEBA, on the other hand, extends visibility to servers, service accounts, and IoT devices. It identifies anomalies such as unusual communication patterns, abnormal resource usage, service execution patterns, and unexpected outbound traffic. This helps detect compromised devices that could otherwise operate unnoticed within the network.
Privacy monitoring for regulated environments
In highly regulated industries such as healthcare, finance, and government, UEBA assists compliance efforts by monitoring access to sensitive data. It tracks who accessed personally identifiable information (PII), protected health records, and financial data, detecting unauthorized or excessive access that may indicate privacy violations. In this way, UEBA helps companies meet regulations such as GDPR, HIPAA, and PCI DSS while supporting effective incident investigations.
Strategic enablement of Zero Trust and compliance frameworks
UEBA supports Zero Trust by continuously validating trust based on behavior rather than one-time authentication. Risk scores generated by UEBA can dynamically influence access decisions and provide the contextual intelligence needed to enforce least privilege. The platform also supports compliance frameworks like NIST, ISO 27001, PCI DSS, and GDPR by maintaining detailed activity logs, demonstrating security controls, and providing evidence of due diligence in protecting sensitive information.
Benefits of implementing UEBA
UEBA transforms security operations from reactive alert management to proactive threat hunting and risk mitigation. It helps enterprises achieve measurable improvements across threat detection, incident response, and compliance.
Detects threats missed by traditional tools
UEBA tools excel at detecting subtle and sophisticated threats that bypass traditional security tools. It can identify insider threats, credential misuse, adversaries who blend into normal network activity, zero-day exploits that lack signatures, compromised legitimate accounts operating within authorized permissions, and data theft. By analyzing behavioral patterns rather than known indicators of compromise, UEBA closes critical detection gaps that attackers exploit.
Provides risk-based prioritization
UEBA assigns contextual risk scores based on factors such as user behavior history, the sensitivity of the accessed resource, peer group comparisons, and concurrent suspicious activities. This risk-based approach allows security operations centers (SOCs) to focus on high-priority threats that represent genuine business risk rather than investigating every minor anomaly.
Enhances response speed and automates containment workflows
By combining real-time analytics, automated workflows, and pre-built playbooks for common threat scenarios, and by integrating with SOAR platforms for orchestrated response, UEBA significantly reduces incident detection and response times. Automated containment actions, such as account suspension, step-up authentication, and access restrictions, can minimize attacker dwell time and limit potential damage.
Improves audit readiness and compliance reporting
Regulatory compliance requires demonstrating continuous monitoring, access controls, and incident response capabilities. UEBA records behavioral data and access activity, maintains audit trails of user activities and access patterns, provides evidence of security controls in operation, generates compliance reports for frameworks like HIPAA, PCI DSS, GDPR, and SOX, and documents investigation processes for regulatory inquiries.
Reduces overall risk exposure and operational cost
By detecting threats early and reducing false positives, UEBA lowers the likelihood and impact of security incidents, such as breach costs associated with data loss, regulatory fines, and reputation damage. At the same time, automation and smarter prioritization reduce manual effort for security teams, helping organizations improve security while controlling operational costs.
Netwrix Identity Threat Detection and Response
The Netwrix Identity Threat Detection and Response (ITDR) solution takes a comprehensive approach to identity security: proactively preventing threats, detecting and containing attacks in real time, and enabling rapid recovery. Rather than relying solely on reactive detection, Netwrix ITDR automatically assesses Active Directory and Microsoft Entra ID for vulnerabilities and misconfigurations, eliminating attack paths before they can be exploited. The solution incorporates behavioral analytics that align with UEBA principles while adding proactive threat blocking to stop identity-based threats like Kerberoasting, DCShadow, password spraying, and Golden Ticket attacks in their tracks.
Netwrix ITDR enhances UEBA-style detection with four key capabilities:
- Proactive risk identification: The solution continuously assesses AD and Entra ID environments for misconfigurations, excessive privileges, and security gaps that attackers exploit. By identifying vulnerabilities before they become attack vectors, security teams can remediate risks at scale rather than reacting to incidents after the fact.
- Proactive threat blocking: Using patented technology, Netwrix ITDR blocks risky changes and unauthorized privileged activity in real time. This includes preventing modifications to Tier 0 groups like Domain Admins, blocking DCSync attempts, and intercepting credential theft techniques before attackers can establish persistence.
- Real-time detection and response: The solution applies behavioral analytics and UEBA principles to detect anomalies across both human users and non-human identities like service accounts. When suspicious activity occurs, whether lateral movement, privilege abuse, or signs of compromised credentials, ITDR generates contextual alerts and can trigger automated containment actions such as disabling accounts or enforcing step-up authentication.
- Rapid recovery capabilities: When attacks do occur, Netwrix ITDR enables quick restoration of AD and Entra ID by rolling back unwanted changes or performing full forest recovery. This minimizes downtime and reduces the business impact of ransomware or destructive incidents, ensuring organizations can resume operations quickly.
Key advantages
- Unified identity protection: Netwrix ITDR protects both AD and Entra ID from a single platform, eliminating tool sprawl and providing complete visibility across hybrid identity environments.
- Faster time to value: With pre-built detection logic for common identity threats, bulk remediation capabilities, and straightforward deployment compared to traditional analytics platforms, organizations can quickly achieve UEBA-aligned insights without extensive customization.
Challenges and considerations
Implementing UEBA requires careful planning and realistic expectations. By understanding the challenges, organizations can avoid common pitfalls.
False positives and tuning
UEBA relies on behavioral baselines, so it requires an initial learning period to accurately distinguish between normal and abnormal activity. During early deployment, organizations may experience higher rates of false positives and alert volumes as the system calibrates normal behavior for each user and entity. Security teams must invest time in tuning detection thresholds, refining risk scoring parameters, and providing feedback on alerts to improve detection accuracy over time.
Privacy and compliance
Because UEBA analyzes user behavior and access patterns, organizations must ensure that data collection and processing comply with privacy regulations such as GDPR and internal acceptable-use policies. This includes implementing appropriate data retention policies, restricting access to behavioral analytics, anonymizing data where possible, and maintaining transparency about monitoring activities.
Deployment complexity
The complexity of UEBA deployment depends on an organization’s data maturity and existing security infrastructure. Integrating multiple data sources, such as identity platforms, endpoints, cloud services, and networks, requires upfront effort. Organizations with fragmented logging systems and inconsistent data formats face steeper deployment challenges than those with well-integrated logging and monitoring environments.
Integration efforts must account for connecting diverse data sources, normalizing log formats across systems, ensuring sufficient network bandwidth for data ingestion, and potentially upgrading infrastructure to handle increased processing demands. Careful planning and phased rollouts help manage this complexity.
Data coverage and quality
UEBA is only as effective as the data it analyzes. Incomplete, inconsistent, or low-quality log data can generate inaccurate baselines, limit detection accuracy, reduce contextual insight, and trigger unreliable alerts. For sound results, organizations should ensure comprehensive, high-quality data coverage from identity systems, endpoints, network infrastructure, cloud services and SaaS applications, and critical business systems.
UEBA in the security stack
UEBA enhances a company’s security stack and overall security posture by adding behavioral intelligence and identity context that other solutions lack. While traditional tools focus on signatures, rules, or network patterns, UEBA analyzes how users and entities actually behave over time.
UEBA, SIEM, EDR, XDR: a quick comparison
The following table presents a comparison between UEBA, SIEM, EDR and XDR.
Capability | UEBA | SIEM | EDR | XDR |
|---|---|---|---|---|
|
Primary focus |
User and entity behavior |
Logs and events |
Endpoint activity |
Cross-domain threat detection |
|
What it analyzes |
Behavioral patterns across users, service accounts, and systems |
Security events and logs from multiple sources |
Processes, files, and activity on endpoints |
Endpoints, network, identities, cloud workloads, email |
|
Detection approach |
ML-driven baselines, anomaly detection, risk scoring |
Rule-based correlation and known indicators |
Signature and behavior-based endpoint detection |
Correlated analytics across multiple security layers |
|
Strengths |
Insider threat detection, account compromise, lateral movement |
Centralized visibility and compliance reporting |
Malware detection and endpoint response |
Unified detection and response with broad context |
|
Limitations alone |
Requires quality data and integrations |
Limited behavioral context, high alert noise |
Narrow endpoint scope |
Depends on quality of integrated signals, can be complex to deploy |
|
How it complements others |
Adds behavioral and identity context |
Acts as a data backbone for UEBA and XDR |
Supplies endpoint telemetry to UEBA and XDR |
Combines UEBA, SIEM, EDR, and NTA insights |
Implementation roadmap
To implement UEBA, organizations must follow a phased, use-case-driven approach that builds a strong foundation for long-term behavioral analytics.
1. Scope and prioritize key use cases
Start by defining the security problems UEBA should address first. Common high-value use cases include insider threats, compromised accounts, and data exfiltration. By focusing on a small number of clearly defined scenarios first, you can validate effectiveness, tune detections, and demonstrate early wins. Organizations should engage security operations, compliance, and business units to ensure that the selected use cases align with potential security risks and business priorities.
2. Ensure data readiness across critical systems
The effectiveness of UEBA depends on high-quality data from across your environment. Before deployment, organizations should verify that logs and activity data are available and reliable across identity systems and IAM platforms, endpoints, email, network traffic, cloud services including SaaS applications, and sensitive data repositories. Logs should contain sufficient details for behavioral analysis, including timestamps, user identities, source and destination information, and action types.
3. Configure baselines and peer analytics during the learning phase
During initial deployment, UEBA requires a learning period to establish behavioral baselines for users and entities. This often spans two to four weeks of normal activity data, though complex environments may require longer periods. During this phase, configure peer groups, such as users with similar roles or access levels, to add context and improve anomaly detection. Security teams should monitor this phase closely and refine settings as patterns emerge.
4. Integrate with SIEM, EDR, IAM, and DLP
Organizations should integrate UEBA systems with their existing security controls to get the most value. Connect UEBA with:
- SIEM to ingest alerts and enrich them with behavioral context.
- EDR platforms to correlate endpoint threats with user behavior.
- IAM systems for real-time access control decisions.
- DLP solutions to enhance data protection with behavioral insights.
These integrations help correlate behavior with events across the entire security stack, providing end-to-end visibility.
5. Define alert routing and investigation workflows
Clear workflows ensure that UEBA alerts are actionable rather than disruptive. Organizations should:
- Define workflows on how alerts are routed, who investigates them, and what response actions are appropriate based on risk levels.
- Establish escalation procedures for high-risk detections.
- Create investigation playbooks that guide analysts through common scenarios.
- Implement automated response actions for clear-cut scenarios like impossible travel or obvious credential compromise to reduce response time.
6. Measure success
Measure UEBA programs using metrics such as mean time to detect threats, false-positive rates, percentage of alerts that lead to confirmed incidents, coverage of critical systems and data sources, and reduction in account compromises and data breaches. Use review insights to refine detection rules, adjust risk scoring, and expand data sources. Continuous improvement keeps UEBA aligned with evolving threats and business operations.
Buyer’s checklist: selecting a UEBA solution
To choose the right UEBA solution from among the many UEBA solutions available, organizations should evaluate whether it supports their security needs and infrastructure. Use this checklist to assess vendors and get lasting value on your investment.
Scalable behavioral analytics across users, devices, and cloud workloads
☐ Supports analysis of user accounts, service accounts, and privileged identities
☐ Monitors endpoints, servers, IoT devices, and network infrastructure
☐ Covers multi-cloud environments including AWS, Microsoft Entra, and Google Cloud
☐ Handles your current data volume with room for growth
☐ Maintains performance as your environment grows complex
Dynamic baselines and peer grouping
☐ Automatically establishes behavioral baselines for each user and entity
☐ Continuously adapts baselines as behaviors evolve
☐ Creates peer groups based on roles, departments, and access patterns
☐ Enables context-driven detection of anomalous behavior using peer comparisons
☐ Allows manual adjustment of peer groups
Transparent risk scoring and prioritization
☐ Provides explainable and actionable risk scores for detected anomalies
☐ Shows which factors contributed to each risk calculation and what behavior contributed to it
☐ Allows customization of risk scoring parameters
☐ Prioritizes alerts based on business impact and threat severity
☐ Reduces alert fatigue through intelligent noise reduction
Integration with existing security stack
☐ Offers pre-built connectors for your SIEM platform (Splunk, QRadar, Sentinel, etc.)
☐ Integrates with EDR, identity systems, cloud IAM, and DLP solutions
☐ Supports standard APIs for custom integrations
☐ Provides clear documentation and integration guides
Automation capabilities for response actions
☐ Triggers automated containment actions for high-risk anomalies
☐ Supports account lockout, session termination, access restrictions, and step-up authentication
☐ Allows customization of automated response playbooks
Privacy and compliance safeguards
☐ Includes data minimization, anonymization, and pseudonymization features
☐ Supports role-based access controls for behavioral data
☐ Provides configurable data retention policies
☐ Complies with GDPR, CCPA, and relevant industry regulations
☐ Generates audit trails and compliance reports
☐ Documents data handling practices transparently
Time-to-value and tuning support
☐ Offers straightforward deployment with minimal infrastructure changes
☐ Includes pre-configured detection models for common threats
☐ Provides reasonable baseline learning period (typically 2-4 weeks)
☐ Delivers quick wins with high-priority use cases
☐ Includes professional services and support for initial tuning
Vendor innovation and roadmap transparency
☐ Demonstrates commitment to product development and enhancement
☐ Shares product roadmap and upcoming capabilities
☐ Maintains active user community and knowledge base
☐ Provides reliable customer support and technical resources
Real-world scenarios
Behavior analytics UEBA proves its value through detection of threats that would otherwise slip past traditional security controls. These practical examples show how behavioral analytics identifies suspicious activity early, turning raw analytics into actionable insight.
Unusual data transfers after hours
A user who typically accesses a limited set of files during business hours suddenly begins downloading large volumes of sensitive data late at night. While no security policy is technically violated, the behavior deviates from the user’s established baseline. Solutions like Netwrix ITDR detect such insider threats in real time by correlating unusual access timing with abnormal data volume and resource sensitivity, alerting security teams to risky activity.
First-time foreign login from a peer group outlier
A successful login occurs from a foreign country, a location that neither the user nor their peer group has accessed from before. It occurs during the user’s normal working hours in the office, creating an impossible travel scenario. Although the credentials are valid, UEBA recognizes this as potential account compromise based on historical behavior, location anomalies, and peer group analysis. Netwrix ITDR detects this deviation and can trigger automated responses (such as step-up authentication and temporary account lockout) through integration with identity and security controls.
Surge in access requests to sensitive repositories
A user suddenly begins accessing sensitive repositories unrelated to their role, triggering a spike in access activity. While the individual requests may appear legitimate in isolation, UEBA correlates this behavior across identity and data systems, comparing it to the user’s baseline and peer group behavior and identifying a potential data exfiltration attempt. Netwrix ITDR supports this use case by correlating identity activity with access to sensitive resources, highlighting abnormal access patterns and privilege misuse that indicate data exfiltration risk. Early detection allows teams to restrict access and assess whether data exposure has occurred.
Multiple failed logins followed by privilege escalation
A service account shows repeated failed authentication attempts across multiple systems, followed by successful login and unexpected privilege escalation. UEBA correlates these events across identity systems and flags the behavior as brute-force activity or lateral movement attempts. The system's risk scoring prioritizes this high-severity chain of events, enabling security teams to contain it quickly. Netwrix ITDR provides contextual insight into the timeline and affected accounts, improving response.
Best practices
Best practices like thoughtful configuration, cross-functional collaboration, and ongoing refinement are essential to effective UEBA software deployment.
Monitor both privileged and non-privileged users
While administrators and privileged accounts pose the highest risk, attackers often target or abuse non-privileged accounts as entry points. UEBA should monitor behavior across all user types, service accounts, and automated processes for comprehensive visibility.
Align alert severity with business impact
Not all anomalies carry the same level of risk. For example, an unusual login to a test environment requires different urgency than abnormal access to financial records. Configure UEBA to map alert severity to business impact, data sensitivity, and user context. This helps security teams focus on incidents that matter most.
Promote cross-team collaboration
Behavioral analytics are most effective when technical findings are enriched with organizational context. Security teams need IT context about planned system changes, maintenance windows, and legitimate administrative activities that might trigger alerts. HR provides information about employee lifecycle events such as role changes, department transfers, and terminations that explain behavioral shifts. Collaboration between security, IT, and HR enables better interpretation of user behavior, reducing false positives while supporting investigations.
Use UEBA as a complementary control
UEBA adds behavioral intelligence to your security ecosystem. When integrated with SIEM, EDR, and IAM solutions, UEBA provides behavioral and identity context that improves detection accuracy and response across the security stack.
Continuously review and refine models
User behavior evolves over time due to role changes, new applications, and shifts in working patterns. Document changes to business processes, organizational structure, and technology platforms that might impact behavioral patterns, and adjust UEBA configurations accordingly. Regularly review baselines, peer groups, and risk scoring models to maintain accuracy.
Proactively prevent threats, detect and contain attacks faster, and recover quickly to keep your business resilient with Netwrix ITDR. Get a demo.
FAQs
Share on
Learn More
About the author

Tyler Reese
VP of Product Management, CISSP
With more than two decades in the software security industry, Tyler Reese is intimately familiar with the rapidly evolving identity and security challenges that businesses face today. Currently, he serves as the product director for the Netwrix Identity and Access Management portfolio, where his responsibilities include evaluating market trends, setting the direction for the IAM product line, and, ultimately, meeting end-user needs. His professional experience ranges from IAM consultation for Fortune 500 companies to working as an enterprise architect of a large direct-to-consumer company. He currently holds the CISSP certification.
