Data Security Posture Management (DSPM)
Find and protect sensitive data, prioritize and root out compliance risks, and shut down risky behavior before it becomes a breach.
Read their Stories
Trusted by
































Sensitive and regulated data is scattered across file shares, cloud platforms, databases, and business apps, leaving most organizations without clear visibility into what they have, where it resides, and how exposed it is. Without accurate discovery and classification, teams can’t prioritize risk, enforce least privilege, apply DLP, or prove compliance.
Proliferation of GenAI
GenAI tools like Copilot and ChatGPT amplify oversharing, exposing sensitive data everywhere.
Scattered shadow data
Shadow data sprawls untracked across cloud, SaaS, and on-prem, creating hidden compliance risks.
Blind spots in data protection
Limited visibility into permissions and activity obscures who can access sensitive information.
Unknown risk exposure
Weak risk assessment tools leave organizations blind to critical threats until breaches occur.
Use cases
Go beyond data security with DSPM solutions
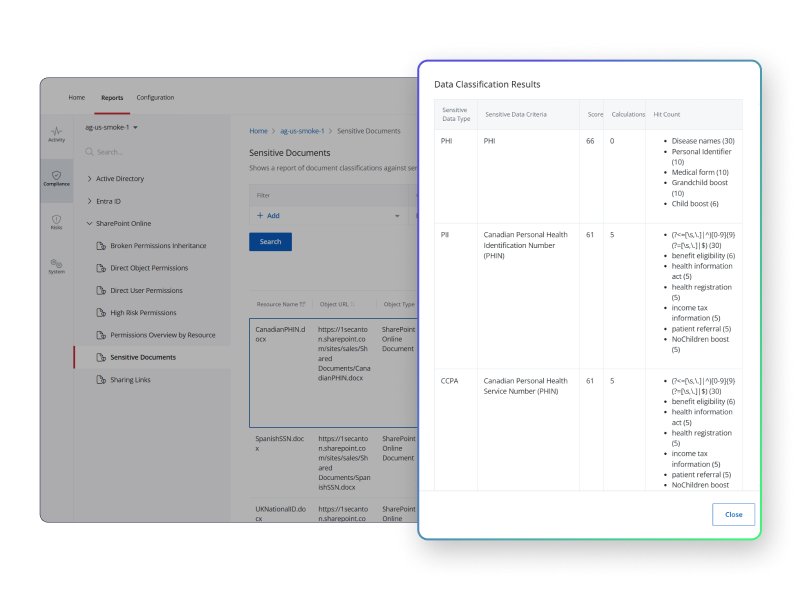
Discover and classify sensitive data
Locate data and perform accurate data classification based on sensitivity, privacy, and compliance requirements. Enhance DLP by accurately tagging sensitive data.
Run data risk assessments
Identify sensitive or high-risk data, evaluate vulnerabilities, such as overexposed data or loose permissions, and prioritize protective measures.
Remediate data exposure
Automatically fix the issues that put data at risk, such as moving assets from insecure storage, updating permissions, or removing sensitive content.
Get visibility into data access
Understand who has access to what, how they are getting that access, and whether they are actually using it. Optimize access controls to uphold the principle of least privilege.
Monitor activity and detect threats
Track and analyze activities to detect unauthorized access, insider threats, or compromised accounts. Automatically fix conditions that put sensitive data at risk.
Make compliance easy
Identify, classify, and manage regulated data to guarantee proper handling, storage, and protection of sensitive data. Implement structured processes for DSARs.
The Netwrix approach
A powerful DSPM solution that secures your data and identities
Get in touch
Let’s talk security
Continuous control of your data wherever it lives
Visibility into data in hybrid environments is impossible without a solid tracking and tagging strategy. The Netwrix Data Security Posture Management solution puts you in charge. Automatically discover and classify hidden data, monitor for threats and suspicious access patterns, and remediate excessive user access issues.

Connect identity and data
Link identity security and data risk management to shore up access privileges and remediate risks through automation.
Full protection across all environments
Deploy full protection for structured and unstructured data, whether you’re cloud, on-premises, or both.
Scalable security for all organizations
Flexibly deploy to any data environment at a level that fits your business size and needs.
Manage data throughout its lifecycle
Identify data types and their sensitivity levels for the implementation of appropriate data retention, data archiving, and data deletion policies.
Trusted by professionals
Don’t just take our word for it
Data Security Posture Management FAQs
Have questions? We’ve got answers.
See DSPM in action