Man-in-the-Middle (MITM) Attacks: What They Are & How to Prevent Them
A man-in-the-middle (MITM) attack is a cyberattack where a hacker intercepts communication between two parties to steal or manipulate sensitive data. Common risks include credential theft, financial fraud, and data breaches. The best defenses include HTTPS, MFA, and secure network practices.
A man in the middle attack often targets login credentials, financial information, and personal data. Attackers use this data for fraud, identity theft, or unauthorized access.
MITM attacks expose gaps in how organizations protect identities and data in transit, resulting in financial loss, credential exposure, operational disruption, and compliance failures.
Attackers often focus on high-value targets such as financial institutions, healthcare systems, SMBs, and cloud services. These environments handle sensitive data like payment details, patient records, and business-critical information. That’s why understanding what is a man in the middle attack, and how it works is essential for reducing risk and protecting data.
Attribute | Details |
|---|---|
|
Attack Type |
Man-in-the-Middle (MITM) Attack |
|
Impact Level |
Critical |
|
Target |
All: Individuals, Businesses, Governments |
|
Primary Attack Vector |
Network, Email, Social Engineering |
|
Motivation |
Financial Gain, Espionage, Disruption, Hacktivism |
|
Common Prevention Methods |
MFA, VPN, HTTPS, Zero Trust, EDR, SIEM, Employee Training |
Risk Factor | Level |
|---|---|
|
Potential Damage |
High |
|
Ease of Execution |
Moderate to High |
|
Likelihood |
Moderate |
Concerned about a Man-in-the-middle attack in your environment?
Speak with our experts to learn practical ways to reduce attack paths and strengthen your security posture.
What is a Man-in-the-middle attack?
A man-in-the-middle (MITM) attack is a type of cyberattack where an attacker intercepts and potentially alters communication between a user and a system without either party knowing. In simple terms, the attacker positions themselves “in the middle” of the two trusted endpoints.
These attacks target data in transit. Their goal is to:
- Steal credentials and authentication tokens,
- Capture financial or personal data,
- Hijack active sessions,
- Inject malicious content into communication.
Unlike phishing or malware attacks, which rely on tricking users or infecting devices, MITM attacks focus on the communication layer itself. The attacker doesn’t need direct access to the system. Instead, they exploit insecure networks, weak encryption, or misconfigured systems.
A common man in the middle attack example is session hijacking. When a user logs in to a website, a session token keeps them authenticated. If an attacker intercepts that token, they can impersonate the user without needing the password.
You may also see this attack referred to as:
- Adversary-in-the-middle (AITM)
- On-path attack
- Machine-in-the-middle
All of these terms describe the same core idea: unauthorized interception of data between two trusted parties in real time.
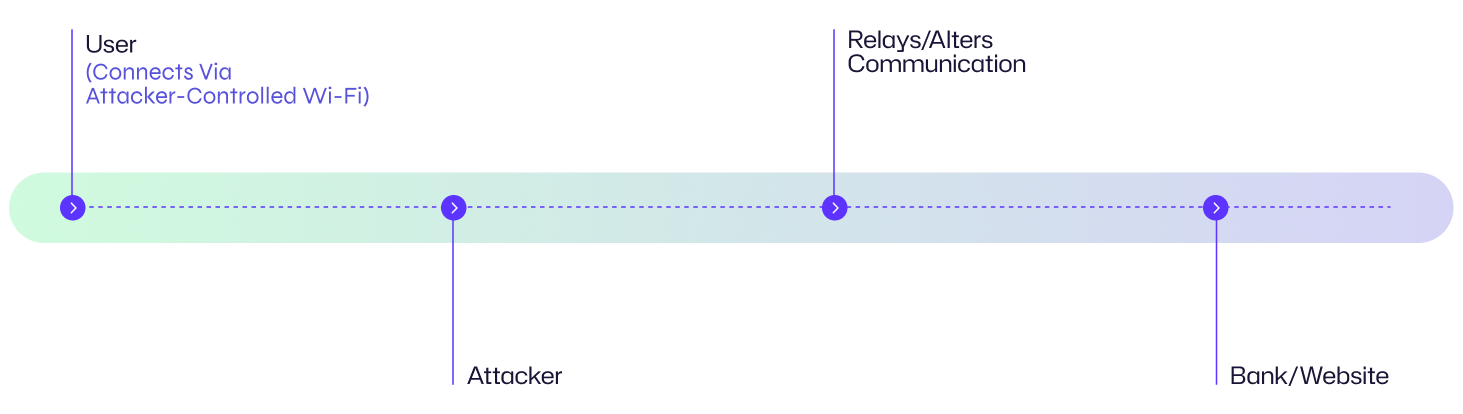
How does a MITM attack work?
A MITM attack typically follows a structured process that allows attackers to intercept, access, and sometimes manipulate data as it moves between systems. Understanding this flow helps security teams identify weak points and reduce exposure.
Before diving into the details, here’s a simplified breakdown of how most man in the middle attacks unfold:
Two key phases of MITM attacks
There are two phases of MITM attack, interception and decryption.
- Interception: This is the first phase, where attackers secretively position themselves between the two communicating parties like inserting a listening device in phone lines without anyone noticing it and later listening to the conversation of two or more parties.
- Decryption: Once an attacker has collected data after interception of communication, the next step is to decipher that data, especially if the communication is encrypted (over HTTPS protocol), as encrypted data is just gibberish without decryption.
Step-by-step breakdown
A typical man in the middle attack in cyber security follows these key stages:
- Reconnaissance
- Interception
- Decryption
- Data capture
- Optional manipulation
- Exit
Reconnaissance
In this initial reconnaissance phase, attackers look for easy entry points. They scan vulnerable networks such as public Wi-Fi in cafés, airports, or hotels.
Common targets include:
- Networks with weak or no passwords
- Routers using default credentials
- Unpatched or poorly configured systems
Attackers also use tools like Wireshark to analyze traffic and map the environment. This helps them identify connected devices, open ports, running services, and potential weaknesses they can exploit.
Interception
After gaining a foothold, attackers position themselves within communication channels to intercept traffic. One common method is setting up rogue Wi-Fi hotspots that mimic legitimate networks, such as a café’s Wi-Fi. When users connect, all their traffic passes through the attacker’s device, allowing them to monitor and capture it.
Attackers may also use Address Resolution Protocol (ARP) spoofing. By sending false ARP messages, they associate their device’s MAC address with the IP address of a legitimate system, such as a router. This redirects traffic intended for the router to the attacker.
Another technique is DNS spoofing, which redirects users to malicious websites. When a user attempts to access a legitimate site, the DNS request is intercepted and redirected to a site controlled by the attacker, enabling further data capture or credential theft.
Decryption
After intercepting encrypted traffic, attackers often seek ways to weaken or bypass encryption to gain access to readable data.
Some common techniques they use include:
- SSL stripping: This involves downgrading a secure HTTPS connection to HTTP. While the user thinks their connection is secure, the attacker can actually view the data in plaintext. Tools like SSLStrip can automate this process.
- Fake SSL certificates: Here, attackers create forged or compromised certificates to impersonate a trusted server. The user’s browser thinks it has established a “secure” connection, but the attacker is in the middle, able to decrypt and monitor the communication.
Data Capture
With successful interception and decryption, attackers then focus on captured data to steal valuable information such as credentials, credit card numbers, bank account details, session cookies, personal information like email, phone numbers and addresses for identity theft.
Several techniques are used to log the data as it is flowing through attacker’s devices and later automated scripts are used to sweep through captured data for sensitive data.
Optional Manipulation
In some cases, attackers just don’t extract data, with sophisticated techniques they can manipulate online banking sessions and alter a transaction such as changing the recipient's bank account and redirect payment to their own account.
Exit
After executing a successful MITM attack, attackers will try to cover their tracks by clearing logs on victim’s devices or servers. In some cases, they will try to install malware or create a backdoor to maintain long-term access to the compromised system or network for data extraction in future.
Man-in-the-middle attack flow diagram
Example Scenarios:
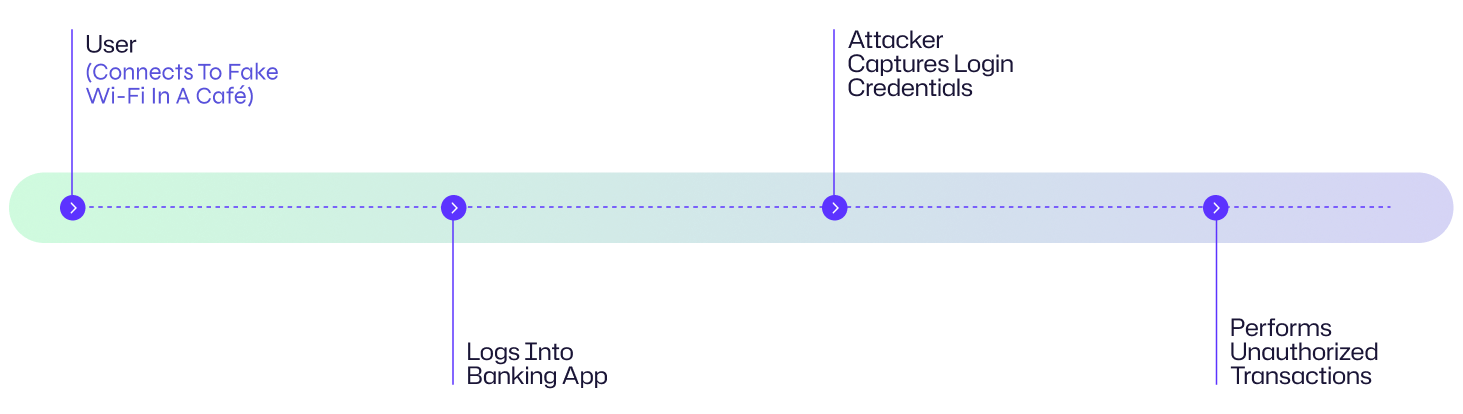
David, a bank employee, connects to an unsecured Wi-Fi network in a public café and unknowingly exposes his connection to a man-in-the-middle (MITM) attack.
He selects a network called “The Rocks” from options including “The Rock,” “Café the Rock,” and “The Rocks.”, while only “Café the Rock” is legitimate. The rogue network is controlled by attackers, allowing them to intercept all traffic from his phone and laptop.
As David logs into social media and banking applications, attackers capture his activity and use SSL stripping to downgrade secure connections. This enables them to access credentials for Facebook, Gmail, and other services.
MFA blocks access to his banking app, but his Gmail and Facebook accounts are not protected. Attackers successfully access his Gmail account, disable notifications, and later run a PPC campaign tied to his account, resulting in an unexpected bill.
Because David uses the same credentials for work, attackers test them against internal systems. An attacker attempts to authenticate and make configuration changes to gain persistence. Security teams are alerted to unauthorized configuration changes across critical systems using Netwrix Change Tracker, allowing them to quickly verify what changed and when. At the same time, abnormal authentication behavior and misuse of credentials are flagged, helping detect account compromise and contain the threat before attackers establish a foothold.
Man in the middle attack examples
Here are some of the most well-known man in the middle attacks and what they reveal about modern security risks.
Case | Impact |
|---|---|
|
DigiNotar (2011) |
Fake SSL certificates issued; widespread data compromise. |
|
Lenovo Superfish (2014) |
Pre-installed adware used MITM for injecting ads. Lenovo added an adware software SuperFish on some of their consumer laptops, which installed a self-signed certificate which was used to inject advertisement into web pages, even on secure HTTPS connections, without user knowledge. The private key of this certificate was the same on every laptop, which allowed attackers to create their own malicious certificates and make it possible to conduct MITM attacks. The Federal Trade Commission (FTC) charged Lenovo with deceptive practices and eventually Lenovo removed SuperFish software. |
|
Equifax (2017) |
Data breach of 145M+ users due to MITM and SSL flaws. |
|
Tesla Wi-Fi exploit (2024) |
Vehicle hijacking via spoofed charging station Wi-Fi. |
These cases show that man in the middle attacks exploit real-world weaknesses in encryption, certificate management, and network security - not just theoretical vulnerabilities.
Consequences of a Man-in-the-middle (MITM) attack
A man-in-the-middle (MITM) attack doesn’t just expose data. It creates a chain reaction of financial, operational, and compliance risks that affect both users and organizations. Some of the impacted areas and the nature of impacts are described below:
Impact Area | Description |
|---|---|
|
Financial |
Data theft, ransom payments, fraudulent transactions. |
|
Operational |
Downtime, service disruption, lost productivity. |
|
Reputational |
Loss of customer trust, brand damage. When a man in the middle attack exposes customer data, trust erodes quickly. Loss of confidence can reduce customer retention, impact revenue, and damage brand credibility long term. |
|
Legal/Regulatory |
Compliance violations (e.g., GDPR, PCI DSS), lawsuits. Data exposure from MITM attacks can trigger compliance violations under frameworks like GDPR, PCI DSS, and HIPAA. This often results in fines, legal action, and mandatory remediation efforts. |
Common targets of MITM attacks: Who is at risk?
Financial Institutes
Financial institutes and online baking are the prime target of MITM attacks due to high value financial data such as login credentials, account details and transaction details. MITM attackers can intercept login attempts, transaction data or alter fund transfer which can lead to financial problems for both end user and institute.
Healthcare Industry
MITM attacks can intercept communication between medical systems and patients to compromise confidential health records for identity theft and insurance fraud, medical history and even manipulation of medical device data.
Small and Medium Businesses
Small and Medium businesses are targeted because they often lack strong cybersecurity infrastructure and can fall victim of MITM attacks due to less secure communication channels, vulnerable outdated networks and systems. Attacker can steal Business data, personal data of customers and gain access to internal systems.
Cloud SaaS Providers
Modern Software-as-Service (SaaS) applications handle a wide range of customers data, if they are not properly configured and secured, MITM attackers take advantage of these services to steal credentials, sensitive data files in case of cloud storage and unauthorized access to business applications.
Industrial IoT Networks
Industrial IoT networks control critical infrastructure like power plants, water treatment facilities, transportation systems and attackers can intercept data being exchanged between devices in IoT networks causing disruption of service, equipment damage or even safety hazards.
Public Wi-Fi Users
Public Wi-Fi Networks are often poorly configured and unsecure, making them favorite targets of MITM attacks. End users connected to these infected or unsecure networks can easily compromise their personal information, browser activity and login credentials.
Risk assessment: How vulnerable are you to MITM attacks?
The risk of a man-in-the-middle (MITM) attack depends on how securely your systems handle data in transit, network access, and user behavior. Not every environment faces the same level of risk from a man-in-the-middle attack.
A practical MITM risk assessment focuses on three factors: likelihood, impact, and existing security gaps.
Here's a list of key risk factors for MITM attacks:
- Unsecured networks - Use of public Wi-Fi or poorly protected internal networks makes it easier for attackers to intercept traffic.
- Weak encryption - Systems that rely on HTTP instead of HTTPS, or outdated TLS versions, are more vulnerable to a MITM attack.
- Misconfigured systems - Incorrect network or DNS configurations can expose communication paths to interception.
- Poor endpoint security - Outdated devices, unpatched software, and lack of endpoint protection create easy entry points.
- Low user awareness - Employees who don’t recognize phishing attempts or unsafe networks increase the risk of a man in the middle cyber attack.
The likelihood of a man-in-the-middle attack increases significantly when:
- Users connect through public or untrusted networks
- Encryption is missing or improperly configured
- Security controls are inconsistent across systems
MITM attacks are becoming more effective due to automation and AI-driven techniques. Attackers can now:
- Scan networks faster
- Identify weak points in real time
- Launch attacks with minimal manual effort
This lowers the barrier to entry and increases the scale of attacks.
It's important to remember that a man-in-the-middle attack in cyber security isn’t just a network issue. It’s a visibility and control problem.
If you can’t clearly see:
- Who is accessing your systems
- How data is moving
- Which connections are trusted
- you can’t effectively reduce risk.
How to prevent Man-in-the-middle attacks
Man in the middle attack prevention requires implementation of different technique combinations, policies and employee’s awareness initiatives.
Here are the most effective ways to prevent a MITM attack:
Use HTTPS and HSTS
Encrypt all communication using HTTPS and modern TLS protocols. This prevents attackers from reading or modifying data in transit.
Enable HTTP Strict Transport Security (HSTS) to enforce secure connections and block downgrade attacks such as SSL stripping. Regularly update SSL/TLS certificates and disable outdated protocols.
Use VPNs on untrusted networks
A virtual private network (VPN) encrypts traffic between the user and the network. This is especially important on public Wi-Fi, where man in the middle attacks are common.
VPNs help ensure that even if traffic is intercepted, it cannot be easily read or altered.
Enable multi-factor authentication (MFA)
Multi-Factor authentication adds an additional layer of security for end users for authentication and authorization process by presenting extra verification factors apart from credentials like authentication apps, security keys or OTP and biometric verification. This reduces the risk of credential misuse, even if credentials are intercepted. Even if an attacker has acquired your username and password, they won’t be able to bypass extra layer of verifications for authentication and access.
Apply Zero Trust and network segmentation
Zero trust is a security framework meaning “never trust, always verify”, assuming that any user account or device can be compromised, must require authentication and authorization before accessing resources.
Zero trust architecture includes implementation of network segmentation by dividing network into secure independent segments, applying least privilege policy like need to access based privileges and continuous verification of user’s identity and monitoring activity patterns.
Secure DNS with DNSSEC, DoH, and DoT
The Domain Name System (DNS) translates human-readable domain names, such as google.com, into IP addresses. MITM attacks often target this process to redirect traffic without the user’s knowledge.
DNS spoofing allows attackers to redirect users to malicious websites by manipulating DNS responses. Instead of reaching a legitimate site, users are silently routed to attacker-controlled infrastructure.
To reduce this risk, organizations can implement DNS security controls such as DNSSEC. DNSSEC helps ensure the authenticity and integrity of DNS responses, making it harder for attackers to tamper with them.
Additional protections, including DNS over HTTPS (DoH) and DNS over TLS (DoT), encrypt DNS traffic between clients and servers. This prevents attackers from intercepting or modifying DNS queries in transit.
Train users to recognize threats
Even with the best technical security measures, a well-crafted phishing email can trick untrained employees to compromise accounts or network segments and thus it is important to invest in employees training.
Employees should understand how to:
- Identify phishing attempts
- Avoid connecting to untrusted networks
- Recognize suspicious login or certificate warnings
Regular training and simulations help reduce the risk of human error leading to a man-in-the middle attack.
How Netwrix helps to prevent MITM attacks
MITM attacks don’t stop at interception. The real risk often begins after attackers compromise credentials.
Netwrix Change Tracker helps security teams detect what happens next by monitoring critical systems for unauthorized configuration changes. If an attacker uses stolen credentials to modify system settings, create persistence mechanisms, or alter security controls, the platform flags those changes with clear context around what changed, when it happened, and who initiated it. This enables teams to investigate faster and contain the threat.
In parallel, teams can detect abnormal authentication behavior such as unusual login patterns or credential misuse early, helping them identify account compromise and stop attackers before they move deeper into the environment.
Prevent Man-in-the-middle attack with Netwrix Change Tracker. Get a demo.
MITM attack detection, mitigation, and response
Detecting a man-in-the-middle attack early and responding quickly limits damage. A strong approach combines user awareness, rapid response, and ongoing security improvements.
Early warning signs
A MITM attack often shows subtle but noticeable signs. Watch for:
- Unexpected connection drops during login or remote sessions
- SSL certificate warnings (expired, invalid, or untrusted certificates)
- Websites loading slowly or appearing altered
- Repeated login prompts despite active sessions
These indicators may signal that communication is being intercepted or manipulated.
Immediate response
If you suspect a man in the middle attack, act quickly to contain the risk:
- Disconnect the affected device from Wi-Fi, VPN, or wired networks
- Change credentials immediately, including passwords, API keys, and access tokens
- Enable MFA on affected accounts if not already in place
- Notify internal teams and stakeholders, including IT, security teams, or service providers
After containment, investigate the scope of the incident by reviewing logs, endpoint activity, and network traffic to identify how the MITM attack occurred.
Long-term mitigation
Reducing the risk of future MITM attacks requires consistent security controls:
- Enforce modern encryption standards such as TLS 1.3 and disable outdated protocols
- Use VPNs for secure remote access
- Deploy IDS/IPS solutions to monitor network traffic
- Implement DNS security controls like DNSSEC
- Regularly update systems, certificates, and security configurations
Strengthen visibility and detection by:
- Reviewing logs across firewalls, servers, and endpoints
- Performing regular penetration testing
- Deploying endpoint detection and response (EDR) tools
User awareness also plays a critical role. Train employees to recognize phishing attempts, certificate warnings, and unsafe networks.
Industry-specific impact of MITM attacks
Man-in-the-middle attacks can have severe consequences across industries, including data breaches, financial fraud, reputational damage, and regulatory penalties.
Industry | Impact |
|---|---|
|
Healthcare |
Patient data breaches, HIPAA fines. MITM attacks can intercept communication between medical systems and patients, exposing sensitive health records. Data breaches can lead both to non-compliance with HIPAA and result in significant fines and legal actions, as well as can be used for patient identity theft, insurance fraud, or manipulation of medical information. |
|
Finance |
Account takeovers, fraudulent transactions, PCI DSS. Financial institutions and online banking are prime targets due to high-value data such as credentials, account details, and transaction information. Attackers can intercept logins or manipulate transactions, leading financial losses and non-compliance with PCI DSS. |
|
Retail |
POS data theft, supply chain vulnerabilities. Retail environments, especially point-of-sale (POS) systems, are vulnerable to MITM attacks that intercept payment data during transactions, harvest credit card details, or sensitive customer data. Attackers can further target partner organizations and suppliers of infected retailers to gain further access to bigger targets. |
Attack evolution & future trends of MITM attacks
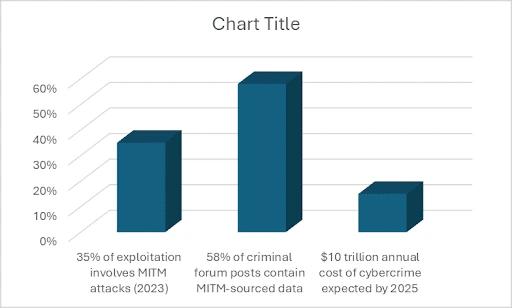
Key statistics and infographics
- MITM attacks remain a common technique, with industry reports suggesting they account for up to 35% of exploitation activity.
- 58% of stolen data leaks on dark web forums are harvested from MITM attacks, which end up being traded and used in criminal activities.
- According to Cybersecurity Ventures, it is predicted in 2020 that the annual cost of cybersecurity measures will grow 15% per year and by 2025 it will reach 10 trillion dollars.
Final thoughts
A man-in-the-middle (MITM) attack targets one of the most critical points in your environment: data in transit. From interception to decryption and manipulation, these attacks exploit gaps in network security, encryption, and user behavior.
Industries like finance, healthcare, retail, and government face higher risk because of the sensitive data they handle. A successful man in the middle attack can lead to financial loss, regulatory penalties, and long-term damage to customer trust.
Reducing risk starts with visibility into how identities and data move across your environment. Organizations should focus on:
- Enforcing secure communication with HTTPS and VPNs
- Strengthening identity protection with MFA
- Monitoring network and endpoint activity
- Securing DNS and preventing spoofing
- Training users to recognize phishing and unsafe networks
There’s no single control that stops every MITM attack. A layered approach - combining encryption, identity security, and continuous monitoring - is key to protecting your environment.
FAQ Section
Share on
View related cybersecurity attacks
Abusing Entra ID Application Permissions – How It Works and Defense Strategies
AdminSDHolder Modification – How It Works and Defense Strategies
AS-REP Roasting Attack - How It Works and Defense Strategies
Hafnium Attack - How It Works and Defense Strategies
DCSync Attacks Explained: Threat to Active Directory Security
Ultimate guide to Golden SAML attacks
What Is a Golden Ticket Attack? How It Works, Detection and Prevention
gMSA exploitation attacks and Golden gMSA attacks explained
DCShadow Attack – How It Works, Real-World Examples & Defense Strategies
ChatGPT Prompt Injection: Understanding Risks, Examples & Prevention
NTDS.dit extraction attacks explained
Pass the Hash Attack
Pass-the-Ticket Attack Explained: Risks, Examples & Defense Strategies
Password Spraying Attack
Plaintext Password Extraction Attack
Zerologon Vulnerability Explained: Risks, Exploits and Mitigation
A complete guide to ransomware attacks
Skeleton Key attack: how it works and how to detect it
Lateral Movement: What Is It, How It Works And Preventions
Kerberoasting Attack – How It Works and Defense Strategies
Why Is PowerShell So Popular for Attackers?
4 Service Account Attacks and How to Protect Against Them
How to Prevent Malware Attacks from Impacting Your Business
What is Credential Stuffing?
Compromising SQL Server with PowerUpSQL
What Are Mousejacking Attacks, and How to Defend Against Them
Stealing Credentials with a Security Support Provider (SSP)
Rainbow Table Attacks: How They Work and How to Defend Against Them
A Comprehensive Look into Password Attacks and How to Stop Them
LDAP Reconnaissance
