A complete guide to ransomware attacks
A ransomware attack encrypts a victim’s files or systems and demands payment to restore access. It can disrupt operations, cause data loss, and lead to significant financial and reputational damage.
Attribute | Details |
|---|---|
|
Attack type |
Ransomware |
|
Impact level |
Critical |
|
Target |
Businesses, governments, healthcare, education, critical infrastructure, SMBs |
|
Primary attack vector |
Phishing emails, exploiting vulnerabilities (RDP, VPN, unpatched systems), stolen credentials, precursor malware, supply chain/MSPs |
|
Motivation |
Financial gain, espionage, disruption, hacktivism |
|
Common prevention methods |
Multi-factor authentication (MFA), patch management, endpoint detection and response (EDR/XDR), firewalls, security awareness training, network segmentation, immutable backups |
Risk Factor | Level |
|---|---|
|
Potential damage |
Critical
|
|
Ease of execution |
Medium-High
|
|
Likelihood |
High |
Not sure how quickly you can detect ransomware activity?
Speak with our experts to strengthen detection and response across your environment.
What is a ransomware attack?
Ransomware is a type of malicious software that blocks access to a computer system or encrypts valuable data until a ransom is paid. It spreads through the network via phishing emails, malicious downloads, and exploitation of unpatched vulnerabilities. Once activated, it locks files or systems and demands payment (mostly in cryptocurrency) to unblock access.
Ransomware is one of the most damaging forms of malware that threatens organizations of all sizes because it directly impacts business continuity, disrupts operations, and causes both financial and reputational harm.
Ransomware variants
Ransomware comes in several forms and types, each using different tactics to pressure victims into paying. These are:
- Encrypting ransomware (crypto): Encrypts files and demands payment for the decryption key.
- Locker ransomware: Denies access to the entire system, locking out users completely.
- Leakware/doxware: Threatens to publish sensitive data if a ransom is not paid.
- Scareware: Displays fake warnings or security alerts to trick users into paying.
- Wipers: Permanently destroys data instead of demanding ransom, causing irreversible loss.
Ransomware has evolved dramatically, from the AIDS Trojan in 1989 (which spread via floppy disks) to WannaCry in 2017 (which crippled global systems using a wormable exploit). By 2025, attackers have adopted triple extortion, which combines data encryption, data leaks, and direct threats to the victims’ customers and partners. This makes modern ransomware more aggressive and far-reaching than ever before.
How does ransomware work?
Ransomware attacks follow a structured lifecycle: infiltrate, encrypt, and extort. By understanding each stage in how ransomware works, organizations can recognize warning signs early and respond before widespread damage occurs.
Step 1: Infection
The attack begins with an initial compromise. Common entry points include:
- Phishing emails with malicious attachments or links
- Drive-by downloads from compromised websites
- Exploitation of internet-facing services such as Remote Desktop Protocol (RDP)
- Abuse of stolen or weak credentials
- Unpatched vulnerabilities in software, VPNs, or third-party services
- Deployment of precursor malware/commodity loaders, such as Emotet, QakBot, Bumblebee
- Compromising managed service providers (MSPs) and supply-chain partners to distribute ransomware widely
Once inside, the malware establishes a foothold in the target environment and proceeds with lateral movement and escalation.
Step 2: Execution
After infiltration, the ransomware executes its payload. It starts by scanning local and network drives for valuable files, deleting shadow copies and backups to prevent recovery, and sometimes stealing credentials for privilege escalation. Some variants use built-in tools like PowerShell or Windows Management Instrumentation (WMI) for stealthy execution. Modern ransomware can also deploy additional tools or scripts to disable security defenses, such as antivirus and other security tools, before proceeding further.
Step 3: Encryption and extortion
This phase of the attack answers the question, what does ransomware do to the files it gets control of? In this phase, the malware uses hybrid encryption to lock critical files and systems. Hybrid encryption combines fast symmetric encryption to secure the data with strong asymmetric encryption to protect the keys, which are controlled by the attackers using a private key. Before or during encryption, attackers steal sensitive data to strengthen their leverage. They then demand payment in exchange for the decryption key needed to unlock the files. Over time, tactics have evolved from single extortion (file encryption) to double extortion (encryption + data theft) and now triple extortion, which adds pressure through threats such as targeting the victim’s customers and partners or launching distributed denial-of-service (DDoS) attacks.
Step 4: Ransom demand
Once encryption is complete, a ransom note appears on infected systems with payment instructions and deadlines. Attackers mostly demand payment in cryptocurrencies such as Bitcoin or Monero for anonymity. To hide their identity and location, they route communication through Tor-based portals. These portals are also used to host ransom payment sites or "leak sites" and provide decryption instructions after payment.
Step 5: Expansion
In advanced attacks, ransomware spreads laterally across the network using stolen credentials and by exploiting domain trust relationships. Attackers then compromise additional endpoints to expand control and encrypt more systems. They may also target or encrypt backups, cloud environments, and connected supply chains to maximize damage and reduce recovery options. These tactics increase an attacker’s bargaining power during ransom negotiations.
Step 6: Outcome
After the attack is complete, the victim either pays (with no guarantee of data recovery) or refuses to pay, opting for recovery through backups, decryptors, and law-enforcement or incident-response support. Each path carries costs, risks, and follow-on actions.
Attack flow diagram
The following diagram and an example-story show the progression of a ransomware campaign from the attacker’s initial intrusion through the eventual business outcomes.
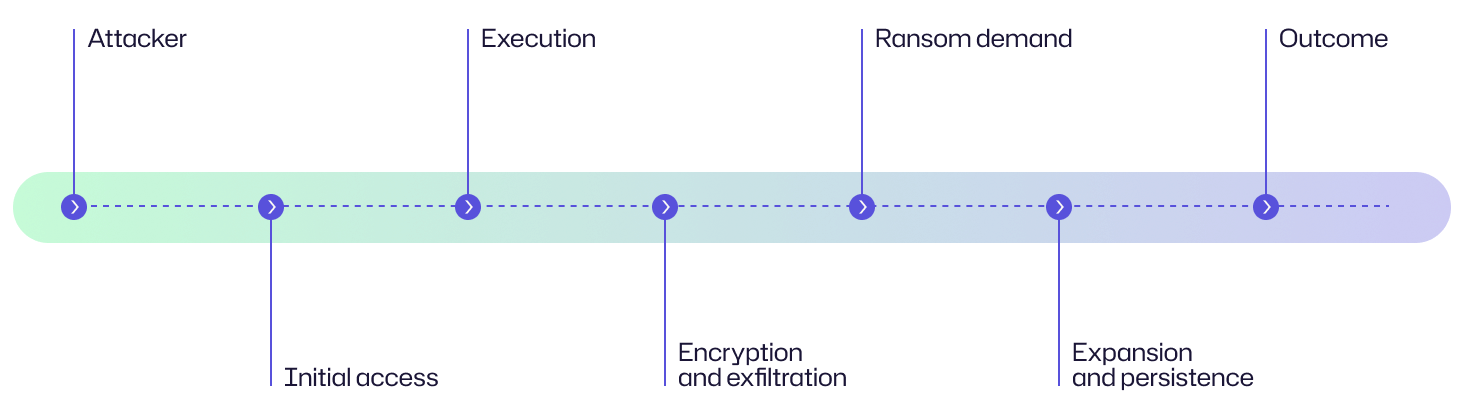
In a financial services company, a ransomware attack began when an employee opened a phishing email that installed malware and gave attackers network access. Soon after, critical files were encrypted, and sensitive data was exfiltrated to attacker servers.
Ransom notes were displayed on affected systems, demanding payment and threatening to leak stolen data. The IT team contained the attack, restored systems from offline backups, and involved law enforcement.
Instead of paying the ransom, the organization rebuilt affected systems and strengthened defenses with better backups, MFA, and staff training.
Examples of ransomware attacks
Here are high-profile, real-world examples of major ransomware incidents that demonstrate different tactics, impacts, and motivations.
Case | Impact |
|---|---|
|
WannaCry (2017) |
The WannaCry attack (2017) exploited the EternalBlue vulnerability in unpatched Windows systems. It quickly spread across more than 150 countries and infected over 200,000 computers within days, with the attackers demanding $300-$600 per infected machine as ransom in many cases. But considering the scale of the infection, few victims paid the ransom. The attack severely disrupted critical sectors such as healthcare, with the UK’s National Health Service (NHS) particularly hard hit. Globally, the total financial impact was estimated between US $4–$8 billion, making WannaCry one of the most damaging cyber outbreaks in history. |
|
NotPetya (2017) |
The NotPetya attack (2017) followed shortly after the WannaCry attack but was far more destructive. It was ransomware that functioned as a wiper, designed to cause irreversible damage rather than collect ransom. It originated in Ukraine through compromised accounting software updates and quickly spread worldwide, crippling multinational companies including Maersk, Merck, Mondelez, and FedEx’s TNT Express. The total global losses exceeded US $10 billion, and Maersk alone reported roughly US $300 million in damages.
|
|
Colonial Pipeline attack (2021) |
In 2021, the DarkSide ransomware group led the Colonial Pipeline attack that struck critical energy infrastructure in the United States. It forced the shutdown of the nation’s largest fuel pipeline for several days, which supplies nearly 45% of the East Coast’s fuel. This triggered fuel shortages, panic buying, and widespread disruption. The company paid US $4.4 million in ransom, part of which was later recovered by the FBI.
|
|
Costa Rica government attack (2022) |
The Costa Rica government attack (2022) showcased how ransomware can disrupt an entire nation. The Conti group targeted 27 government agencies, including the Ministries of Finance and Labor, disrupting economic activity, tax collection, export/import services, customs, and salary payments. The Costa Rican president declared a national state of emergency as the attack caused estimated damages exceeding US $200 million. |
Consequences of ransomware attacks
Ransomware attacks have far-reaching consequences that go beyond data encryption and ransom payments. Their effect on an organization’s finances, operations, reputation, and legal standing can create long-term challenges.
Impact area | Description |
|---|---|
|
Financial |
Ransomware incidents cause significant financial strain through direct ransom payments, costs of forensic investigation, system restore, and extended downtime. Even if organizations do not pay ransom, they face millions in incident response, recovery expenses, lost revenue, and legal penalties. In addition, victims may encounter higher cyber insurance premiums.
|
|
Operational |
Disruption in business processes and operations is immediate and severe. Critical systems become inaccessible, resulting in halting production lines, supply chain operations, and essential services. Organizations may have to revert to manual processes, which are inefficient and slow. Recovery efforts can take days or weeks, impacting productivity and business continuity.
|
|
Reputational |
Ransomware incidents can also damage an organization’s reputation. Customers lose confidence in the company’s ability to protect their data, and negative media coverage can erode public trust. Long-term effects include customer attrition, difficulty attracting new customers, and strained relationships with partners and investors.
|
|
Legal/regulatory |
Ransomware attacks can trigger legal and regulatory consequences. Theft of sensitive data can result in violations of data protection laws such as GDPR or HIPAA, forcing the organization to report the breach and face possible investigations, lawsuits, and regulatory fines. In regulated industries, such breaches can also lead to suspension of licenses, extra compliance audits, and penalties from oversight bodies. |
Common targets of ransomware attacks: Who is at risk?
Let’s be candid, any organization that relies on digital systems to store data or deliver services can succumb to a ransomware attack. However, certain industries face higher risks due to the value of their data, the critical nature of their operations, or their limited cybersecurity resources. Here are some of the most common targets of ransomware attacks.
Healthcare organizations
Hospitals, clinics, and medical research institutions are prime targets for ransomware attackers. These organizations handle highly sensitive patient data such as electronic health records (EHRs) and personally identifiable information (PII). Because healthcare systems must remain operational to ensure patient safety, attackers exploit this urgency to force victims to pay ransom.
Government and public sector
Municipalities, ministries, and state agencies manage critical citizen services like tax collection, public safety, and utilities. Ransomware attacks on these entities can paralyze essential operations, unfold large-scale disruption that affects entire communities, and erode public trust. Many government bodies still operate legacy systems and have poor cybersecurity budgets, making them easy targets for cybercriminals.
Education sector
Schools, universities, and research facilities hold vast amounts of personal data belonging to students, staff, and alumni, as well as valuable research data that can attract cybercriminals. The rise of remote and hybrid learning during the COVID-19 pandemic has further expanded their attack surfaces. With limited IT budgets and increasing digital dependencies, many educational institutions have become frequent victims of ransomware, facing costly downtime, data theft, and the potential loss of critical research work.
Financial institutions
Banks, insurance companies, and fintech firms attract attackers due to their access to financial assets and sensitive customer data. A breach can benefit them with direct monetary gain and valuable stolen information for fraud or resale. Moreover, the financial sector has to adhere to strict compliance regulations, which amplify the consequences of a ransomware incident through penalties, customer loss, and reputational harm.
Critical infrastructure
Energy providers, utilities, transportation networks, and telecommunications companies form the backbone of society. A ransomware attack in this sector can cause far-reaching disruption, such as halting fuel distribution, cutting power, or disabling communication systems. The 2021 Colonial Pipeline attack, for instance, led to widespread fuel shortages in the US, highlighting how ransomware can have national-level consequences.
Small and medium-sized businesses (SMBs)
SMBs are among the most frequent ransomware victims. Many lack the budgets to implement advanced security infrastructures, making them appealing “low-hanging fruit.” Attackers prefer to exploit them as stepping stones in supply chain attacks to infiltrate bigger targets. The financial impact on SMBs can be crippling, as prolonged downtime and ransom demands may threaten their survival.
Manufacturing and retail
Factories, logistics providers, and retail companies depend on interconnected systems such as POS (point of sale) terminals, supply chain software, and production networks. A ransomware attack can halt manufacturing lines and freeze e-commerce transactions, leading to massive revenue losses. Attackers take advantage of these situations, where every hour of downtime costs businesses money.
Risk assessment
To understand the risk level of ransomware attacks, you need to evaluate their potential impact, ease of execution, and overall likelihood. Here is a discussion of each risk factor and its justification.
Risk factor | Level |
|---|---|
|
Potential damage |
Critical
|
|
Ease of execution |
Medium to High
|
|
Likelihood |
High According to Statista, 72.7% of organizations globally reported being affected by ransomware in 2023. |
How to prevent ransomware attacks
To prevent ransomware attacks, companies should implement a defense strategy that combines strong technical controls, employee awareness, and proactive planning. No single tool can stop an attack, but organizations can greatly reduce their risk exposure by addressing vulnerabilities across systems, credentials, and human behavior.
Internet-facing systems
Attackers have been observed to exploit exposed services and unpatched systems to gain initial access. Organizations should:
- Apply regular patches and updates to operating systems, web applications, and firmware to close known vulnerabilities.
- Disable outdated protocols such as SMBv1, which are abused in ransomware propagation.
- Conduct routine vulnerability scans and penetration tests to identify weak points.
- Limit public access to remote management ports (such as RDP, SSH) and use VPNs or secure gateways for remote connections.
Credentials
Compromised credentials serve as an easy entry point for ransomware operators. Organizations should:
- Enforce phishing-resistant MFA, especially for privileged and remote accounts.
- Adopt identity and access management (IAM) controls to manage user permissions and automate provisioning/deprovisioning.
- Use password managers to generate and store strong, unique passwords.
- Admins should use a regular account for daily tasks and only switch to their admin accounts when they actually need administrator privileges, to limit the risk of lateral movement.
Phishing and social engineering
Phishing is the most widely used ransomware delivery method. To build your defenses:
- Train employees to recognize phishing emails, fake login pages, and suspicious attachments.
- Implement email authentication standards such as DMARC, SPF, and DKIM to block spoofed domains.
- Filter email attachments and links using sandboxing and advanced threat protection tools.
- Conduct simulated phishing exercises to test and reinforce awareness.
Endpoint protection
Endpoints are prime targets for ransomware payloads. To protect them:
- Deploy endpoint detection and response (EDR) tools to monitor behavior and block malicious activity in real time.
- Implement application whitelisting and blacklisting to prevent unauthorized executables from running.
- Use intrusion detection systems (IDS) and Sysmon configurations to log and analyze suspicious system events.
- Centrally manage and regularly update all endpoint agents.
Backups
You must devise a robust strategy to back up your systems and data. This will help you recover quickly from an attack and minimize damage. Because attackers attempt to delete backups, you should make sure backups are stored securely.
- Maintain offline or immutable backups that cannot be altered or deleted by attackers.
- Create golden images of critical systems so that they can be restored quickly.
- Use cloud-to-cloud backup solutions for SaaS and cloud workloads.
- Secure the systems where your backups reside using identity and access management (IAM) systems such as MFA and firewalls.
- Test backup restore processes regularly to ensure that they work when needed.
General hardening
Strengthen your overall security posture to reduce the attack surface.
- Adopt a zero trust architecture, where every user and device must be verified regardless of location.
- Segment networks to contain potential ransomware spread between departments or systems.
- Maintain an asset inventory to track all devices, software, and services connected to your environment.
- Limit administrative privileges and enforce the principle of least privilege across all accounts.
Precursor malware and endpoint protection
Many ransomware attacks are preceded by other malware, such as TrickBot, Emotet, or QakBot, which prepare systems for ransomware deployment. Organizations should:
- Use centrally managed antivirus and EDR solutions with heuristic and behavioral detection.
- Implement application whitelisting and blacklisting to block unapproved scripts and executables.
- Monitor with intrusion detection systems (IDS) and Sysmon configurations for early warning signs.
- Act quickly to remove malware at an early stage and isolate affected systems to stop the attack from spreading.
Third parties and managed service providers (MSPs)
Attackers like to target trusted vendors and MSPs to reach multiple clients at once.
- Draw contracts that clearly state security obligations for any third party that handles your data or infrastructure.
- Apply least-privilege access for vendors to limit network visibility for them.
- Require secure cloud practices (SCPs) such as dedicated accounts, encryption, and multi-tenant isolation in cloud environments.
- Continuously monitor vendor activity and access logs for anomalies.
Preparing for ransomware incidents
Even with the best defenses, organizations must be prepared for ransomware incidents. Your readiness determines how quickly you can recover.
- Develop and test an incident response plan (IRP) that defines roles, escalation paths, and containment procedures.
- Create an internal and external communications plan that should include media and customer notifications.
- Save copies of critical contacts and IRP documents offline. These may include executives, IT staff, law enforcement (such as FBI and CISA), and relevant Information Sharing and Analysis Centers (ISACs).
- Understand the data breach notification requirements under state, federal, and international laws.
- Define the role of cyber insurance and legal counsel to guide ransom decisions and post-incident recovery.
How Netwrix can help
Netwrix offers a suite of security tools that strengthen your defenses and improve incident response against ransomware. While Netwrix Threat Manager serves as the frontline defense, the company’s other solutions also protect against ransomware by strengthening visibility, limiting blast radius, and enabling faster recovery.
Netwrix Threat Manager
Threat Manager delivers real-time threat detection and automated response.
- It continuously monitors both file system and identity-related activities in real time. It detects ransomware-like behaviors (such as mass file operations, suspicious RMM tool usage, unusual writes or deletions, and abnormal encryption patterns) through its advanced threat models. The application also identifies privilege escalation attempts, account anomalies, and suspicious authentications across Active Directory, and integrates seamlessly with Microsoft Entra ID for hybrid environments.
- It triggers automated containment actions, such as disabling compromised accounts, resetting passwords, ending active sessions, and marking accounts as “compromised.”
- It also raises real-time alerts that are delivered via email or mobile notifications.
- It can also be integrated and customized via PowerShell scripts, webhooks, and SIEM/alerting systems (Slack, ServiceNow, Teams).
- Threat Manager extends protections to Microsoft Entra ID in addition to on-prem AD environments.
Netwrix Threat Prevention
Threat Prevention adds a preventive layer by alerting or blocking suspicious changes in Active Directory, risky authentication events, and critical object changes before they escalate into breaches.
Netwrix Endpoint Protector
Endpoint Protector provides endpoint control and prevents data loss. It monitors and controls data transfer by blocking rogue USB and other unauthorized devices, and controlling file transfers. It also enforces encryption and can even work offline, mitigating the risk of data exfiltration.
Netwrix Auditor
Auditor tracks and reports on system changes, user activity, and file modifications. It gives you visibility into who did what and when, which is useful in detecting early signs of ransomware activity and post-incident investigation.
Detect and respond to ransomware with Netwrix Threat Manager. Download free trial.
Detection, mitigation and response strategies
Organizations that detect and respond to ransomware attacks quickly can limit damage and recovery time.
Detection
Early detection is important to stop ransomware infection before it spreads. Security teams should continuously monitor systems and networks for warning signs such as:
- Suspicious file activity, including mass file renaming, encryption, or deletion of shadow copies (which are used for system restore).
- Abnormal network traffic, like unexpected spikes in data transfer or communication with known command-and-control (C2) servers.
- Credential dumping attempts using tools like Mimikatz or LSASS access.
- Unusual remote monitoring and management (RMM) tool activity or Cobalt Strike beacons, which may indicate lateral movement or attacker persistence.
EDR, SIEM, and Sysmon solutions enable proactive monitoring, which can help detect these indicators early and trigger alerts for investigation.
Mitigation steps
On detecting a ransomware incident, security teams must act swiftly to contain the threat and preserve evidence. IT, legal, and executive teams must coordinate to ensure an effective and compliant response.
- Isolate infected systems (individual computers, servers, etc.) immediately from the network to prevent further spread.
- If needed, take affected network segments offline to cut them off from communication with uncompromised devices. Do this when you suspect that the compromise has spread across multiple devices within a particular network segment, or when you cannot immediately identify all affected systems.
- After identifying and disconnecting infected devices, use anti-malware tools to remove the ransomware. Avoid resuming normal operations until all systems are clean, as hidden malware can reappear and infect more files.
- Once you are confident that your network is free of ransomware, run a full system scan to uncover any remaining malware that could cause problems after recovery.
- Try to locate the source of the ransomware or malware. This will make it easier to determine how the infection spreads. Ask employees about any unusual behavior they have noticed on their computers or if they have clicked any attachments or links in suspect emails.
- Preserve forensic evidence, including system images, memory dumps, and log files, for later analysis and investigation.
- Notify appropriate authorities, such as the FBI, CISA, or your sector’s Information Sharing and Analysis Center (ISAC).
Response
After containing the threat, the focus shifts to restoring systems and preventing recurrence:
- Reset all passwords and revoke compromised credentials to block attacker access.
- Patch the exploited vulnerabilities and harden systems to close security gaps.
- Perform a clean rebuild of affected machines using golden images (trusted system baselines verified to be malware-free).
- If the backup files have been hacked or deleted, look for potential decryptors. Several organizations provide support with free tools and programs that can help decrypt data, as discussed in the Resources and government support section.
- Share indicators of compromise (IOCs) with the broader community via trusted platforms like StopRansomware.gov or your sector’s ISAC. This can help others defend against similar attacks.
Should you pay the ransom?
The FBI, CISA, and NSA strongly advise organizations not to pay the ransom. Paying carries serious risks.
- There is no guarantee that data will be decrypted or that attackers will not strike again.
- Payments fund criminal operations and encourage further attacks.
- Some ransomware groups are sanctioned entities, meaning payment could violate federal laws and trigger penalties.
Instead of paying, consider safer alternatives such as:
- Restore from secure backups maintained offline or in immutable storage.
- Use free decryptors available from the No More Ransom project.
- Engage law enforcement, who may assist in recovery or in negotiating with the attackers without violating regulations.
The UK government has gone as far as to propose a ban on ransom payments, under which public sector bodies and operators of critical national infrastructure (including the NHS, local councils, and schools) would be prohibited from complying with ransom demands.
Resources and government support
Organizations do not have to face ransomware alone. Many government and industry resources provide assistance, intelligence, and recovery tools.
|
US government agencies |
|
|
Free public resources |
|
|
Guidance frameworks |
|
|
Sector ISACs |
By joining an industry-specific ISAC, organizations can share intelligence, receive timely alerts, and coordinate defense efforts across their sector. You can explore the full list here: National Council of ISACs |
Industry-specific impact
Ransomware affects every sector differently, but its consequences are universally severe. Each industry faces unique operational, financial, and regulatory risks that can disrupt services, damage reputation, and erode public trust.
Industry | Impact |
|---|---|
|
Healthcare |
A ransomware attack can cripple hospital operations by encrypting or blocking access to electronic health records (EHRs), which can lead to delayed surgeries and disrupted patient care. If protected health information (PHI) is exposed, it can trigger HIPAA violations, leading to costly fines. Organizations may also suffer long-term reputational damage. |
|
Finance |
Attacks on financial institutions can result in the theft of financial data, unauthorized transactions, and prolonged service outages. These incidents lead to financial losses, PCI DSS compliance failures, and erosion of customer confidence.
|
|
Government |
Ransomware targeting government agencies can halt critical public services such as emergency response, transportation, and utilities. This sector is highly targeted because interfering with critical infrastructure, like electricity or water, can cause widespread chaos. Exposure of citizen data and classified information can pose national security risks and diminish public trust in institutions. |
|
Education |
Schools, universities, and research institutions store vast amounts of personal and research data. Attacks can disrupt classes, expose student and staff records, and encrypt valuable intellectual property for ransom.
|
|
Manufacturing |
Manufacturers depend on continuous production lines and connected industrial systems (IoT and SCADA). A ransomware attack can stop operations, leading to major financial losses. Because downtime is so costly, many companies prefer to pay the ransom quickly to resume production.
|
|
Technology and IT services |
Tech companies and service providers are attractive targets since they manage data and infrastructure for multiple clients. A single compromise can spread through the supply chain and affect hundreds of organizations. Attackers exploit this leverage to cause broader disruption and demand higher ransom. |
How Netwrix Data Classification can help
By classifying and tagging sensitive data (healthcare records, financial information, government data) across on-premises and cloud environments, Netwrix Data Classification enables organizations to redirect protection and backup efforts to what matters most. The solution can also simplify compliance activities. It maps and tags data subject to regulations (HIPAA, GDPR, PCI DSS), making it easier to generate reports, respond to data subject requests, and prove data handling policies.
Attack evolution and future trends
Ransomware attacks are likely to become faster, more adaptive, and more automated. Due to the rising use of AI, expansion into cloud environments, and targeting of critical infrastructure, it will become harder for organizations to detect and contain the attacks. By staying ahead of ransomware trends, organizations can prepare equally strong defenses to encounter the threat.
Key statistics and infographics
Ransomware attack numbers and ransom demands have been rising year after year. The following key statistics and graphs highlight recent trends and financial impacts, offering a data-driven look at why ransomware remains a top concern for organizations in every sector.
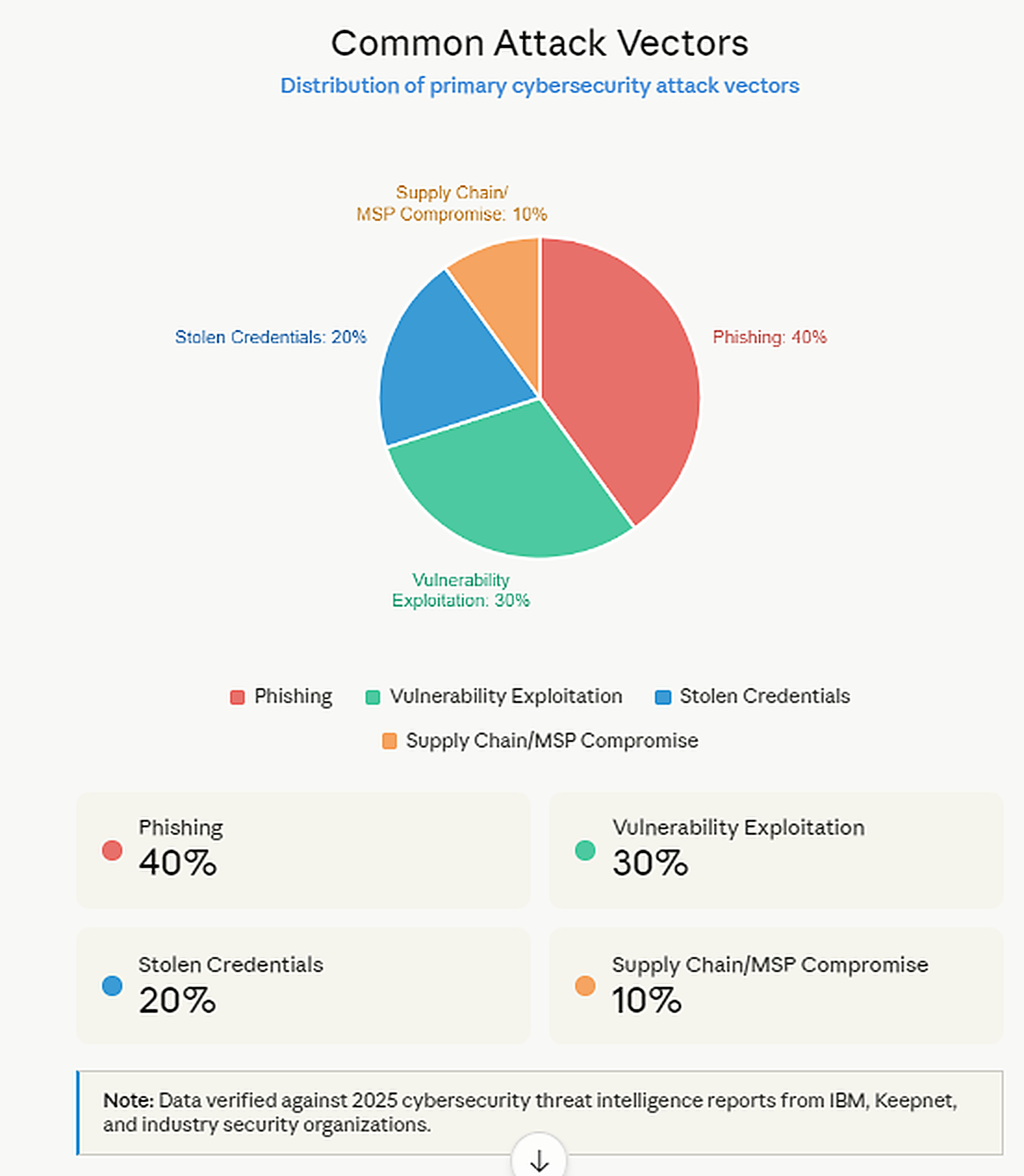
- Research shows that phishing is indeed a dominant attack vector. Guardz’s 33 Phishing Attack Statistics in 2024 claims that 9 out of 10 data breaches in 2023 originated from phishing attacks targeting employees.
- StationX states that phishing is the most common method for delivering ransomware, responsible for 45% of all ransomware attacks.
- Ransomware was responsible for over 70% of reported cyber incidents in 2023, as reported by Cyberint. However, Bright Defense mentions that in 2024, ransomware accounted for 32% of reported malware incidents, showing a significant drop.
- Average ransom payments increased significantly in 2024. For example, Sophos reports that the average ransom payment rose from about $400,000 in 2023 to roughly $2 million in 2024 for organizations that paid, indicating a sharp increase from previous years. However, total payments dropped notably in 2024, both in overall value and in the proportion of victims who paid, even as ransom demands remained high.
- Global ransomware damages are projected to cost $265 billion annually by 2031. These estimates are based on widely cited predictions that the price tag will increase 30% every year.
- Healthcare remains the #1 most targeted industry, followed by finance, government, and education. According to the FBI's 2024 Internet Crime Report, healthcare had more cyberthreats last than any other critical infrastructure industry. With 444 reported incidents, 238 were ransomware threats. However, critical manufacturing had more ransomware incidents, with 258.
Pie chart showing common attack vectors
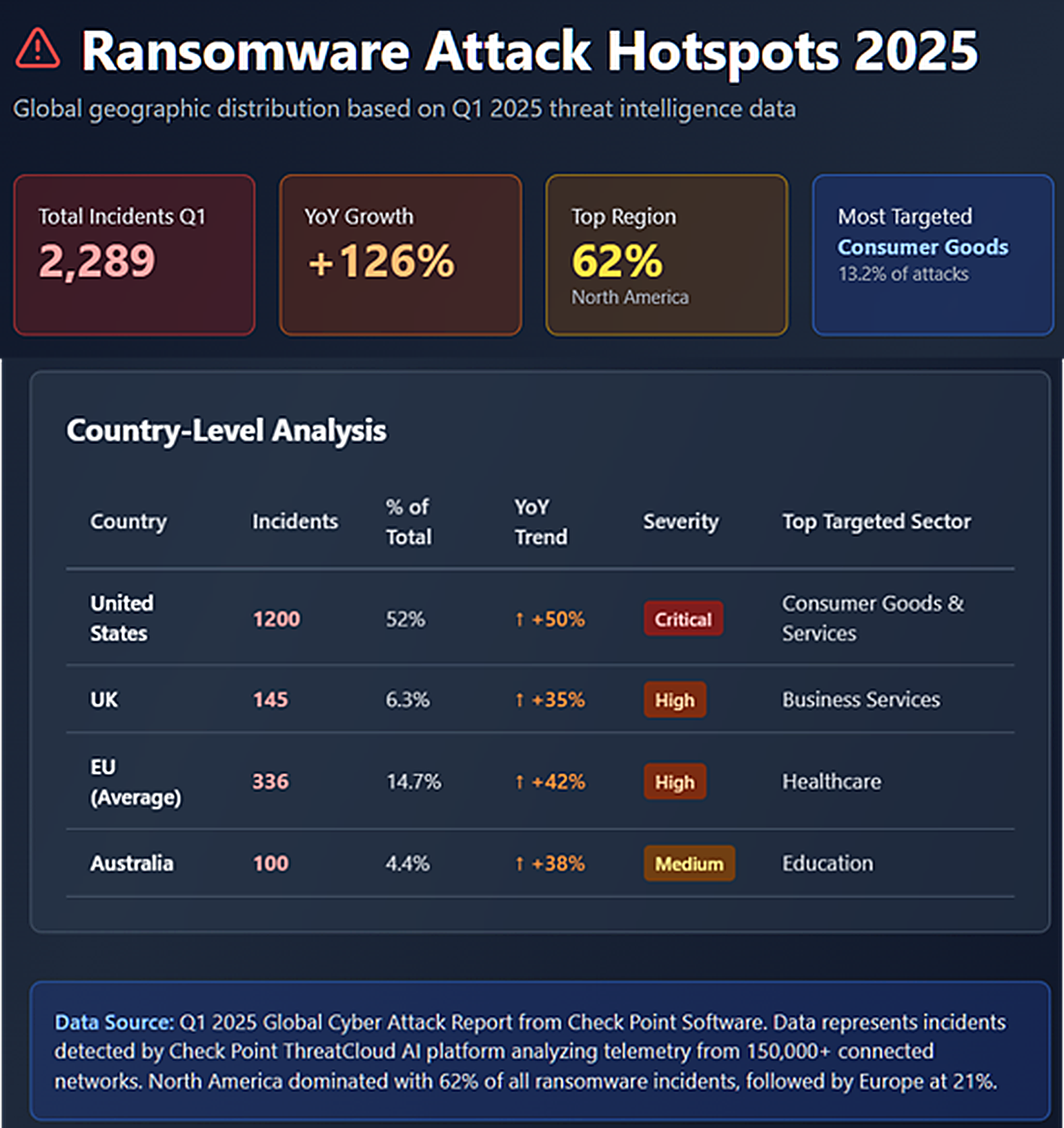
Geographic hotspots of ransomware attacks (US, UK, EU, Australia)
Final thoughts
Let’s get back to what ransomware attacks are. The definition of a ransomware attack does not just represent its criminal implications. It also hints at a battle for control in an age where data defines power.
No organization is immune to the threat, regardless of size or industry. While the statistics are sobering, the good news is that most ransomware attacks are preventable.
The fight against ransomware cannot be won with a single solution, but rather through a combination of technical controls, employee awareness, and a proactive security mindset. In the end, survival will depend not on who avoids the next attack, but on who is prepared to recover from it.
FAQs
Share on
View related cybersecurity attacks
Abusing Entra ID Application Permissions – How It Works and Defense Strategies
AdminSDHolder Modification – How It Works and Defense Strategies
AS-REP Roasting Attack - How It Works and Defense Strategies
Hafnium Attack - How It Works and Defense Strategies
DCSync Attacks Explained: Threat to Active Directory Security
Pass the Hash Attack
What Is a Golden Ticket Attack? How It Works, Detection and Prevention
gMSA exploitation attacks and Golden gMSA attacks explained
DCShadow Attack – How It Works, Real-World Examples & Defense Strategies
ChatGPT Prompt Injection: Understanding Risks, Examples & Prevention
NTDS.dit extraction attacks explained
Kerberoasting Attack – How It Works and Defense Strategies
Pass-the-Ticket Attack Explained: Risks, Examples & Defense Strategies
Password Spraying Attack
Plaintext Password Extraction Attack
Zerologon Vulnerability Explained: Risks, Exploits and Mitigation
Skeleton Key attack: how it works and how to detect it
Silver Ticket Attack
Lateral Movement: What Is It, How It Works And Preventions
Man-in-the-Middle (MITM) Attacks: What They Are & How to Prevent Them
Why Is PowerShell So Popular for Attackers?
4 Service Account Attacks and How to Protect Against Them
How to Prevent Malware Attacks from Impacting Your Business
What is Credential Stuffing?
Compromising SQL Server with PowerUpSQL
What Are Mousejacking Attacks, and How to Defend Against Them
Stealing Credentials with a Security Support Provider (SSP)
Rainbow Table Attacks: How They Work and How to Defend Against Them
A Comprehensive Look into Password Attacks and How to Stop Them
LDAP Reconnaissance
Bypassing MFA with the Pass-the-Cookie Attack
Ultimate guide to Golden SAML attacks
