Skeleton Key attack: how it works and how to detect it
A Skeleton Key attack occurs when malware implants an in-memory "master" credential, or password, into an authentication system so an attacker can sign in with that credential while leaving all AD accounts intact.
Attribute | Details |
|---|---|
|
Attack type
|
Skeleton Key malware: Active Directory authentication bypass |
|
Impact level |
Critical
|
|
Target |
Businesses, government, organizations using Active Directory
|
|
Primary attack vector |
Compromised domain controller or administrative access
|
|
Motivation |
Financial gain, espionage, disruption
|
|
Common prevention methods |
Timely patching, least privilege access, EDR, SIEM, enhanced AD monitoring |
Risk factor | Level |
|---|---|
|
Potential damage |
Critical |
|
Ease of execution |
Medium |
|
Likelihood |
Medium to high |
Concerned about Skeleton Key attacks in your Active Directory?
Speak with our experts to learn how to detect unauthorized access and protect privileged credentials.
What is Skeleton Key malware?
Skeleton Key malware is a stealthy, in-memory backdoor that alters Active Directory’s authentication process, enabling an attacker to authenticate by using a single “master” credential (password). It does not steal or replace user passwords; it changes the authentication logic on a domain controller to accept the forged master credential with any valid username.
To alter the authentication process, malware injects malicious code into LSASS (Local Security Authority Subsystem Service) on a compromised domain controller, which patches or hooks the authentication routine. Once implanted, LSASS will accept the attacker’s master credential during authentication requests, effectively letting the attacker sign in as any existing user. Because this check occurs in LSASS memory, the master credential does not need to be recorded in the Active Directory database (NTDS.dit). Active Directory remains unchanged and normal credentials continue to work, making the implant hard to spot.
There’s a catch here, though. If an Active Directory site has multiple domain controllers, the Skeleton Key implant must be present on each DC to ensure that the Skeleton Key master password is accepted as the user’s valid password. Clients discover a domain controller using DCLocator, which effectively picks a domain controller at random. So if a client happens to authenticate to a domain controller that does not have Skeleton Key installed, the master password will fail.
The normal authentication process and how Skeleton Key bypasses it
Skeleton Key does not bypass the account existence check; it only bypasses the password validation step. When a user signs in:
- The DC first checks if the username exists in Active Directory (this step is not bypassed).
- Next, LSASS normally asks AD (or the authentication package) to validate the supplied password against stored hashes or Kerberos keys. This is where Skeleton Key intervenes. Before the normal validation occurs, the malicious code looks for the attacker’s master credential (special password or token). If it is presented, LSASS returns success and the login proceeds (even though no such credential exists in Active Directory).
In short, Skeleton Key allows the master password to be accepted as valid for any existing account. The account itself must be a legitimate AD user object.
Attack severity
The primary goal of a Skeleton Key attack is to maintain persistent, undetected, near-total domain access to a network, with the attacker moving laterally and misusing privileges without having to compromise accounts. Because the modification is in memory, detection requires EDR and memory forensics, LSASS integrity checks, and careful AD and behavioral monitoring rather than just file scans or password-change logs.
How does Skeleton Key malware work?
Here is a walkthrough of the Skeleton Key attack lifecycle and what each stage practically means.
Initial compromise
The attack begins when an attacker gains privileged access to a domain controller or an account with permissions to install code on a domain controller. Common vectors of an initial breach include spear-phishing, stolen or reused credentials, exploitation of an unpatched vulnerability, or misuse of remote admin tools (RDP, VPNs, remote management consoles).
Malware deployment
After gaining access, the attacker normally uploads the Skeleton Key DLL file to a staging directory on a jump host in the victim's network. Next, they use privileged credentials, such as Domain Administrator, to copy the Skeleton Key binary to the domain controller and execute it to inject it into the LSASS process. LSASS handles Windows authentication, so by injecting code that patches or hooks the authentication routine in memory, the malware can intercept authentication requests in memory. It does not modify files or change user password hashes in Active Directory; instead, it changes what the domain controller accepts during authentication. As a result, the domain controller will still report normal authentication behavior for legitimate credentials, while also accepting the backdoor master password.
Once Skeleton Key is successfully deployed, attackers delete the Skeleton Key DLL file from the targeted domain controllers and from the staging directory on the jump host.
Authentication override
With its code running inside LSASS, the malware intercepts login attempts and implements a bypass: if a presented password matches the attacker’s secret “master” password, the domain controller returns a successful authentication for whatever username was supplied. In this way, the attacker can authenticate as any domain account (including highly privileged accounts). Because the attack does not modify password hashes stored in Active Directory, standard password audits and directory inspections will show nothing wrong, making this override stealthy and dangerous.
Lateral movement
Armed with a master password, the attacker can impersonate any user and request Kerberos tickets, access services, and RDP into hosts. This capability accelerates privilege escalation and lateral movement across the environment. Actions that otherwise require time-consuming credential theft or compromise can now be quickly accomplished, allowing an attacker to reach sensitive systems before defenders realize the breach.
Persistence
A Skeleton Key attack remains active until the domain controller or LSASS process is restarted, since a reboot removes the in-memory hooks. However, that does not guarantee that the attacker no longer has footholds. For example, attackers may already have created rogue AD accounts as a fallback or installed other persistence mechanisms such as scheduled tasks, malicious services, or registry-based backdoors that survive reboots. They may also re-compromise the domain controller and re-deploy malware.
Covering tracks
Attackers focus on blending their activity into normal traffic to avoid detection. They use legitimate admin tools (Living off the Land) to avoid introducing new artifacts, use normal protocols and accounts, mimic typical login patterns, tamper with or delete logs, and avoid noisy behaviors (for example, limit high-volume or unusual activities).
Attack flow diagram
Here is a visual flow of the Skeleton Key attack and an example story from an organization’s perspective that shows the typical chain of events, from an initial compromise to user impersonation, until attackers reach valuable data and exfiltrate it.
Attacker → Initial compromise → LSASS injection → Authentication override with master password → Lateral movement → Data exfiltration
Imagine Acom Manufacturing, which relies on Active Directory for identity and access. An attacker targets a helpdesk admin who reused credentials from a breached site. Using those credentials, the attacker logs into a management workstation, escalates access to a domain controller, and deploys Skeleton Key malware. With the master password accepted by the domain controller, the attacker requests Kerberos tickets, accesses file servers, deploys tools to collect sensitive IP and financial records, and exfiltrates the data without changing any AD password hashes.
Examples of Skeleton Key attacks
The Skeleton Key attack appears in a handful of technical analyses and threat-intelligence reports, but publicly available disclosures with victim names are rare. Many organizations and vendors treat these intrusions as sensitive and withhold details. The most widely documented incident is the Taiwan semiconductor and government attack.
Case | Impact |
|---|---|
|
Dell SecureWorks' Counter Threat Unit (CTU) discovery of Skeleton Key (Jan 2015) |
CTU researchers discovered a malware family on a customer network and published the first public technical analysis in January 2015. They named it ‘Skeleton Key’ and described how it patches domain controllers in memory to accept an attacker-chosen password for any account. CTU observed that two 64-bit DLL variants were used in deployments. The malware lacked persistence on disk and was removed after a DC reboot, so attackers redeployed it after reboots. |
|
Operation Skeleton Key: Taiwan semiconductor and government attacks |
Taiwanese cybersecurity firm CyCraft reported a targeted, multi-victim cyber-espionage campaign where APT actors used Skeleton Key-style malware to bypass authentication and maintain persistent access for data exfiltration without triggering password-based alerts, primarily targeting intellectual property. Timeframe: Late 2018 to late 2019 Suspected threat actor: APT Chimera, a suspected China-based threat group Primary targets:
Attack objectives: The main objective was the exfiltration of intellectual property, such as documents on integrated circuits (IC), software development kits (SDKs), IC designs, and source code. Technical details:
|
Consequences of Skeleton Key attacks
Since Skeleton Key malware compromises the core of an organization’s authentication system, its impact extends beyond a single incident, with far-reaching consequences that affect an organization’s operations, finances, and reputation.
Impact area | Description |
|---|---|
|
Financial
|
Organizations may face direct financial losses from theft or fraudulent transactions facilitated by unauthorized access. Additional costs include forensic investigations, system restoration, security improvements, and potential ransom or extortion payments. |
|
Operational |
By compromising domain controllers, attackers can gain access to nearly every system and user account. This can disrupt authentication services, hinder daily business operations, and require extensive remediation efforts to restore trust in Active Directory infrastructure.
|
|
Reputational |
A breach of this scale can damage customer and partner trust. News of a compromised authentication system, especially in financial or government sectors, can lead to negative publicity and tarnish brand repute. |
|
Legal/regulatory |
Unauthorized access to sensitive data may trigger mandatory breach disclosures and investigations by regulatory bodies. Non-compliance with data protection laws such as GDPR, HIPAA, or other regional regulations can result in significant fines and legal action. |
Common targets of Skeleton Key attacks: Who is at risk?
Skeleton Key attacks mostly target organizations that rely on Active Directory for authentication. These attacks are especially effective against large, complex IT environments where detecting subtle authentication anomalies can be difficult. Here are some of the most common types of organizations at risk:
Large enterprises with AD environments
Large enterprises with AD environments Large organizations with extensive Active Directory infrastructures present ideal conditions for Skeleton Key attacks. Multiple domain controllers, distributed sites, and thousands of user accounts create a broad attack surface that cannot be monitored consistently.
Organizations with single-factor authentication
Organizations with single-factor authentication Skeleton Key exploits weaknesses in password-based authentication. This means that companies that have not implemented MFA and rely solely on passwords for authentication are particularly vulnerable because the malware bypasses standard credential checks.
Entities with many privileged accounts
Administrators, service accounts, and IT staff have elevated permissions across systems. Each high-privileged account increases the chance for an attacker to impersonate a high-value identity to access sensitive data, deploy further payloads, and disable security tools. Hence, companies with a greater number of privileged accounts are more attractive targets.
Government agencies and critical infrastructure
Public-sector networks and critical infrastructure entities (such as energy, defense, and telecommunications) are high-value targets for threat actors, particularly for espionage. By compromising domain controllers in these environments, attackers can gain wide-reaching access to classified data and operational systems.
Organizations without strong endpoint or memory monitoring
Skeleton Key operates entirely in memory and does not persist on disk, so antivirus solutions fail to detect it. Networks that do not have advanced endpoint detection and response (EDR) or memory integrity monitoring are less likely to detect the intrusion.
Companies with outdated Windows Server versions
Older or unpatched Windows Server installations have weaker defenses and limited logging or visibility into LSASS processes. These weaknesses give attackers more opportunities to inject and maintain the Skeleton Key malware.
Risk assessment
Skeleton Key poses a significant risk to organizations because it compromises Active Directory, which is the very foundation of network authentication.
Risk factor | Level |
|---|---|
|
Potential damage
|
Extremely high |
|
Ease of execution |
Medium |
|
Likelihood |
Medium to high |
How to prevent Skeleton Key attacks
To prevent Skeleton Key attacks, organizations need a mix of strong access controls, proactive monitoring, and security measures to protect authentication systems.
- Apply the latest patches: Keep domain controllers and authentication systems up-to-date with security patches to prevent exploitation of known vulnerabilities. Patching reduces the attack surface and closes entry points that attackers might use to gain the initial foothold.
- Enforce least privilege: Limit administrative rights to only those who truly need them. Implement role-based access control (RBAC), use just-in-time privileged access management, and apply MFA to all admin accounts. Administrators should use separate accounts for routine work and administrative tasks, and perform all privileged operations from hardened, isolated workstations.
- Monitor LSASS activity: Continuously watch for unusual behavior in LSASS, such as memory access or process injection attempts, which are indicators of Skeleton Key attacks.
- Implement advanced endpoint protection: Deploy an endpoint detection and response (EDR) solution that can detect in-memory attacks, suspicious syscalls, and credential manipulation that antivirus may miss.
- Leverage SIEM correlation: Use a security information and event management (SIEM) platform to correlate suspicious authentication attempts, especially multiple successful authentications with mismatched source IPs or logins outside business hours.
How Netwrix can help
Netwrix offers solutions that can help defend against credential-based attacks, including Skeleton Key, through detection, access controls, and monitoring.
Netwrix Threat Manager
The Threat Manager application empowers organizations to guard against Skeleton Key attacks with the following capabilities:
- Uses behavioral analytics and heuristics to detect in-memory attacks (including Skeleton Key and other credential-stealing tools).
- Deploys deception-based detection, such as decoys and honeytoken credentials, to lure attackers and generate alerts when they are used.
- Correlates suspicious events and anomalies (such as unusual login attempts, lateral movement patterns, honeytoken credential use) to flag possible credential or memory attacks.
Netwrix Threat Prevention
The Threat Prevention application includes capabilities specifically designed to monitor and protect the LSASS process (which is a prime target for Skeleton Key and other credential-stealing tools).
- The LSASS Guardian Monitor feature watches for unauthorized handle requests (read, write, thread creation) that come from non-whitelisted processes targeting LSASS, and generates alerts when suspicious memory-access operations are observed.
- When an untrusted process tries to open a handle to the LSASS process with read, write, or thread creation permissions, Threat Prevention’s LSASS Guardian Protect feature will intercept that request and block malicious in-memory attacks without crashing the process.
Netwrix Identity Threat Detection & Response (ITDR)
The Threat Manager and Threat Prevention software is part of the Netwrix ITDR solution. Overall, the ITDR platform offers robust functionality that:
- Monitors privileged identity behavior (administrative accounts, service accounts) for anomalies in authentication patterns, unusual login times, source IPs, and impersonation attempts.
- Flags credential abuse, credential impersonation, and suspicious account usage patterns in a way consistent with Skeleton Key tactics.
- Provides full audit trails and session histories to support incident investigation.
Netwrix Privileged Access Management (PAM)
The Privileged Access Management solution helps minimize the window in which attackers can exploit privileged accounts. Using it, organizations can:
- Enforce just-in-time (JIT) access, granting elevated privilege only when needed and revoking it soon after.
- Apply zero standing privilege, so that no high-level accounts are in constant use.
- Implement role-based access control (RBAC) to limit the degree to which accounts can move laterally or escalate, as well as limit the scope and lateral movement potential of high-privilege sessions.
Detect and respond to Skeleton Key attacks with Netwrix Identity Threat Detection & Response. Download free trial.
Detection, mitigation and response strategies
To defend against Skeleton Key attacks, organizations must detect in-memory manipulation at the earliest stages, swiftly contain any compromise, and eliminate persistence.
Detection
Skeleton Key operates entirely in-memory and does not generate network traffic, which is why it barely leaves traces in conventional logs and evades conventional network-based IDS/IPS detection. Therefore, monitoring and behavioral analytics are essential to identify suspicious activity that indicates compromise. Organizations should consider the following:
- Perform memory analysis on domain controllers to detect LSASS code injection or unauthorized modules. Tools such as Volatility, Sysinternals RAMMap, and EDR telemetry can identify anomalous DLLs or injected threads. Specifically, look for unsigned modules, modules loaded from unexpected file paths (such as temporary directories), or hooks placed on authentication functions. Organizations should establish a baseline of normal LSASS memory state, which may help them identify deviations indicating potential compromise.
- Correlate authentication anomalies, which can spot the use of the Skeleton Key master credential. Monitor security event logs and authentication servers for patterns such as successful logons where incorrect passwords were entered.
- Monitor for Kerberos ticket requests that deviate from normal patterns. For example, requests for service tickets without corresponding Ticket-Granting Ticket (TGT) requests or repeated TGS-REQs from unexpected hosts.
- Inspect Windows event logs for unusual LSASS access or unexpected service restarts. Key Event IDs include 4624 and 4672 for privileged logon sessions, 4688 for suspicious process creation with LSASS interaction, and 7036 and 7034 for service state changes or unexpected terminations. Any non-system process accessing LSASS memory is a red flag.
- Integrate with SIEM and ITDR tools (for example, Netwrix Threat Manager and Threat Prevention) to correlate behavioral anomalies, credential misuse, and memory-level indicators of compromise. Configure detection rules that correlate multiple weak signals into high-confidence alerts, such as privileged account activity from unusual geolocations or outside business hours combined with LSASS memory access alerts. This approach filters out false positives while catching attacks that bypass single-point detection mechanisms.
- SecureWorks CTU observed a subtle operational symptom of a Skeleton Key attack. Shortly after the deployment of the malware, domain controllers experience unexplained Active Directory replication failures. These are issues that Microsoft support could not explain or resolve definitively until the domain controllers were rebooted. Organizations should consider such replication anomalies a potential red flag of a hidden compromise.
- CTU researchers also developed YARA signatures to help detect the Skeleton Key DLL and the specific code it injects into the LSASS process memory. Using these signatures with endpoint detection tools and forensic scanners can help identify in-memory artifacts of Skeleton Key infections. This is one of the few reliable technical methods for detection.
Mitigation steps
Mitigation focuses on reducing the attack surface, strengthening authentication controls, and deploying defenses that prevent attackers from injecting code or obtaining elevated privileges. Organizations should implement the following controls:
- Apply the latest security patches to all domain controllers and authentication systems to eliminate known privilege escalation vulnerabilities. Give preference to updates that address remote code execution, privilege escalation, and LSASS-related vulnerabilities.
- Enforce MFA for all privileged accounts, including Domain Admins, Enterprise Admins, and service accounts with elevated permissions. They should also extend MFA requirements to administrative protocols such as RDP, PowerShell remoting, and domain controller console access, as well as all remote access solutions like VPNs and webmail. MFA does not fully block a Skeleton Key attack, but it can reduce the risk of unauthorized access and lateral movement across the network.
- Restrict Domain Admin and Enterprise Admin privileges to only essential personnel and enforce just-in-time (JIT) elevation through PAM solutions. Allow time-bound sessions that automatically revoke elevated permissions after task completion.
- Deploy in-memory attack detection tools such as Netwrix Threat Prevention (LSASS Guardian) or EDR agents to monitor and block unauthorized access to LSASS in real time.
- Harden Active Directory configurations through the following measures:
- Disable unnecessary services on domain controllers (such as Print Spooler, Server service if not required).
- Implement service control policies that prevent unauthorized service restarts or modifications.
- Disable accounts that are no longer needed.
- Audit and restrict delegation settings to prevent attackers from abusing delegation.
- Enable Advanced Audit Policy Configuration to capture detailed authentication and privilege use events.
- Segment administrative workstations using privileged access workstations (PAWs) to ensure that administrative sessions occur in isolated, controlled environments. Consider implementing credential tiering (tier 0 for domain controllers, tier 1 for servers, tier 2 for workstations) to prevent credential theft from lower tiers affecting higher-privilege systems.
Response
A quick and well-planned incident response is critical if you suspect a Skeleton Key infection. The goal is to contain the breach, restore the integrity of the authentication mechanism, and remove persistence.
- Isolate the affected domain controller from the network immediately to prevent lateral movement and further credential misuse. If multiple domain controllers are suspected of compromise, isolate them simultaneously. Before isolation, capture a memory dump of the LSASS process for forensic analysis, as this evidence will be lost upon reboot or shutdown.
- Remove the malware by performing a trusted system rebuild or restoring from verified clean backups. After removal, verify that LSASS is operating normally by checking loaded modules, monitoring authentication behavior, and confirming that no unauthorized code remains in memory. This ensures that LSASS and Active Directory integrity is restored.
- Rotate all privileged credentials, including Domain Admin, service, and KRBTGT passwords, to invalidate any stolen or forged tokens.
- Perform a full Active Directory audit to detect unauthorized group memberships, privilege changes, or persistence backdoors (such as Golden Ticket or SIDHistory abuse). Tools such as Netwrix Auditor can help identify unusual privilege relationships and misconfigurations.
- Conduct a forensic investigation using endpoint forensics and Active Directory logs to identify the root cause and scope of compromise. Focus on evidence of LSASS memory access, unauthorized logons, and credential dumping tools.
- Reinforce long-term monitoring post-incident with ITDR and SIEM correlation rules tuned for LSASS access and abnormal authentication patterns.
Industry-specific impact
Skeleton Key attacks can have severe and varied consequences across industries, depending on the sensitivity of their data. Whatever the industry, the attack grants attackers unrestricted access to critical systems, enabling large-scale data theft and disrupted operations.
Industry | Impact |
|---|---|
|
Healthcare
|
Attackers can gain unauthorized access to patient records, electronic health systems, and prescription data. This can lead to HIPAA violations, identity theft, and loss of patient trust. Compromise of authentication systems may also disrupt medical services and hospital operations. Attackers may also manipulate medical records and alter treatment plans, potentially endangering patient safety. |
|
Finance |
By authenticating as any user, an attacker can alter financial records, make unauthorized fund transfers, launder money, manipulate internal banking systems, and abuse the SWIFT network. This can lead to regulatory and reputational damage. Financial institutions may face severe penalties from regulatory bodies, compounded by volatility in stock prices and long-term customer attrition. Attackers may also exploit trading systems to manipulate markets, making detection and recovery extremely difficult.
|
|
Government |
Skeleton Key infections in government networks can lead to classified data theft, espionage, and sabotage of essential services like power grids and water treatment facilities. Attackers may impersonate privileged users to access restricted systems and exfiltrate sensitive intelligence data. Such breaches have long-term geopolitical implications. |
Attack evolution and future trends
Threat actors are increasingly integrating the Skeleton Key technique into larger, multi-stage attack campaigns to maintain persistence, escalate privileges, and take control of the domain. New automated tools and AI-powered evasion techniques are making these attacks faster to deploy, harder to spot, and easier to spread. Here are some recent trends:
Key statistics and infographics
Let’s look at some facts and visuals that capture the scale and impact of Skeleton Key attacks.
- In earlier Skeleton Key cases (around 2013 to 2015), researchers observed Skeleton Key being used in conjunction with Backdoor.Winnti, which suggests that it was part of broader intrusion and backdoor tool usage.
- A HYPR/Vanson Bourne report from 2022 found that financial institutions experienced an average of $2.19 million in annual losses from breaches related to authentication weaknesses.
- According to IBM's 2024 Cost of a Data Breach Report, breaches resulting from stolen or compromised credentials took the longest to identify and contain, with an average duration of 292 days. This allows attackers nearly 10 months of unrestricted access before discovery.
- Experts strongly agree that recovery costs for domain controller compromise are significantly higher than standard breaches due to the need for complete Active Directory reconstruction.
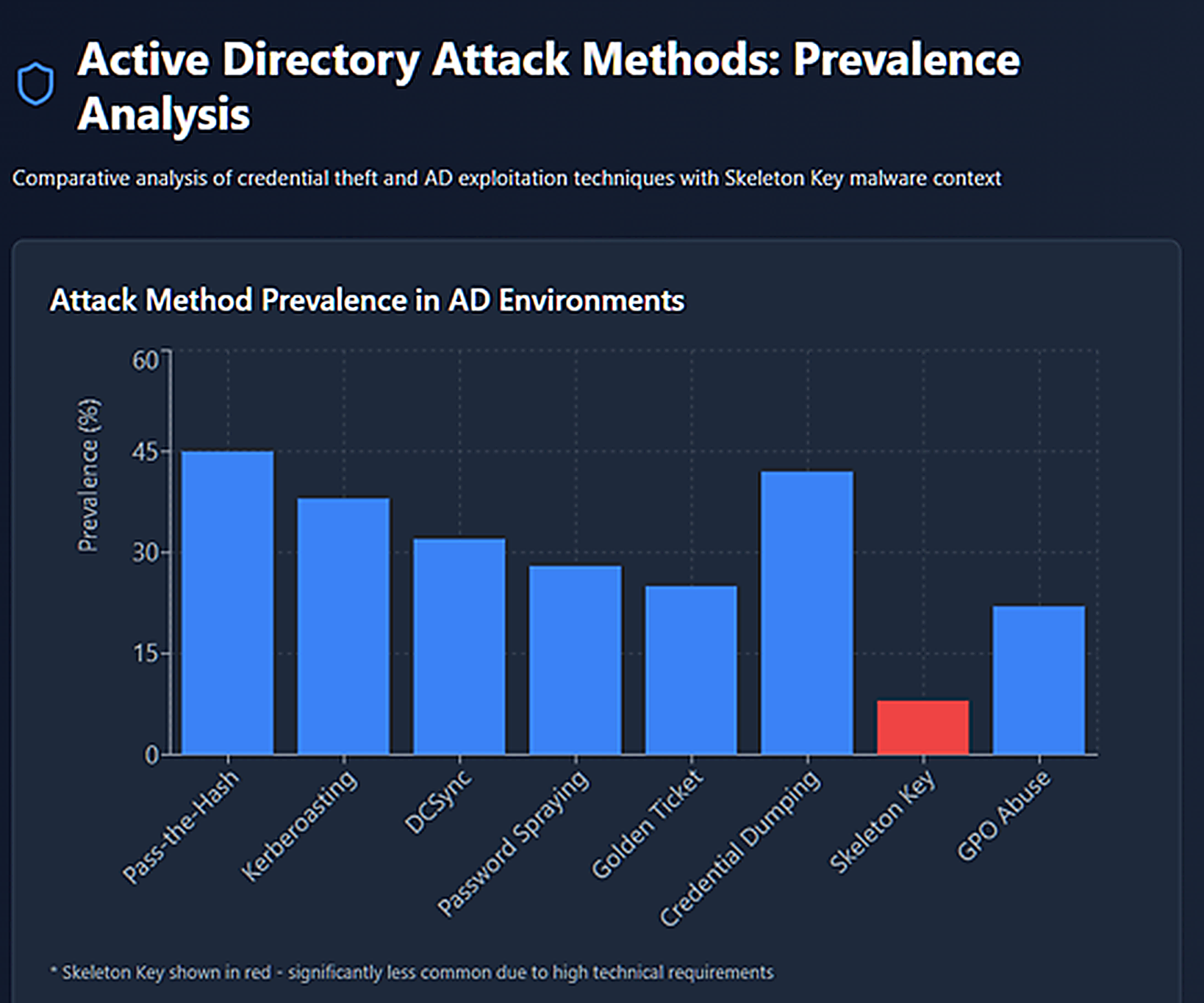
Active Directory attack methods: prevalence analysis
The following graph shows Skeleton Key malware at only 8% prevalence, making it less common than other Active Directory attacks. Pass-the-Hash (45%), credential dumping (42%), and Kerberoasting (38%) are far more prevalent because they are easier to execute and do not require prior admin access.
Final thoughts
Like the skeleton keys of old that could unlock any door in a building, the Skeleton Key attack gives threat actors unrestricted access to your entire domain. Once inserted into your Active Directory, this digital master key opens every account, bypasses every password, and grants unlimited entry, silently and invisibly.
The difference? In the physical world, you would notice if someone was picking your locks. But in your network, a Skeleton Key can stay hidden for months, quietly turning while your security team watches the front door. The good news is, this attack leaves traces. With proper monitoring, patching, and privileged access controls, you can detect the attack and slam the door shut before real damage occurs.
Your domain security is only as strong as your weakest authentication point. Make sure a Skeleton Key cannot open it.
FAQs
Share on
View related cybersecurity attacks
Abusing Entra ID Application Permissions – How It Works and Defense Strategies
AdminSDHolder Modification – How It Works and Defense Strategies
AS-REP Roasting Attack - How It Works and Defense Strategies
Hafnium Attack - How It Works and Defense Strategies
DCSync Attacks Explained: Threat to Active Directory Security
Pass the Hash Attack
What Is a Golden Ticket Attack? How It Works, Detection and Prevention
gMSA exploitation attacks and Golden gMSA attacks explained
DCShadow Attack – How It Works, Real-World Examples & Defense Strategies
ChatGPT Prompt Injection: Understanding Risks, Examples & Prevention
NTDS.dit extraction attacks explained
Kerberoasting Attack – How It Works and Defense Strategies
Pass-the-Ticket Attack Explained: Risks, Examples & Defense Strategies
Password Spraying Attack
Plaintext Password Extraction Attack
Zerologon Vulnerability Explained: Risks, Exploits and Mitigation
A complete guide to ransomware attacks
Silver Ticket Attack
Lateral Movement: What Is It, How It Works And Preventions
Man-in-the-Middle (MITM) Attacks: What They Are & How to Prevent Them
Why Is PowerShell So Popular for Attackers?
4 Service Account Attacks and How to Protect Against Them
How to Prevent Malware Attacks from Impacting Your Business
What is Credential Stuffing?
Compromising SQL Server with PowerUpSQL
What Are Mousejacking Attacks, and How to Defend Against Them
Stealing Credentials with a Security Support Provider (SSP)
Rainbow Table Attacks: How They Work and How to Defend Against Them
A Comprehensive Look into Password Attacks and How to Stop Them
LDAP Reconnaissance
Bypassing MFA with the Pass-the-Cookie Attack
Ultimate guide to Golden SAML attacks
