NTDS.dit extraction attacks explained
In an NTDS.dit extraction attack, adversaries exfiltrate the Active Directory database file from a domain controller and dump credential material. They then crack and reuse credentials for widespread and persistent access across the network.
Attribute | Details |
|---|---|
|
Attack type |
Credential access (NTDS.dit extraction) |
|
Impact level |
Critical, full AD compromise possible |
|
Target |
Domain controllers (AD DS) |
|
Primary attack vector |
Privileged access + NTDS.dit exfiltration |
|
Motivation |
Espionage, ransomware, persistence |
|
Common prevention methods |
Admin tiering, MFA for privileged accounts, krbtgt rotation, encrypted backups, monitoring for shadow copy activity |
Risk factor | Level |
|---|---|
|
Potential damage |
Critical |
|
Ease of execution |
Medium |
|
Likelihood |
Medium-High |
Sensitive directory data at risk in your environment?
Speak with our experts to learn how to detect NTDS.dit access and protect critical identity data.
What is NTDS.dit and its role in Active Directory?
The NTDS.dit file is the primary database of Active Directory (AD) that stores critical information about all AD objects, such as users, credentials, computers, groups and their memberships, and password hashes. This data enables authentication, authorization, and directory services across a Windows domain, which is why attackers often target this file in credential theft campaigns.
Here are some interesting facts about the NTDS.dit file:
- By default, the NTDS.dit file is located at: C:\Windows\NTDS\ntds.dit.
- Technically, NTDS.dit is built on the Extensible Storage Engine (ESE), a lightweight database engine that organizes its contents into tables, indexes, and transaction logs for fast queries and reliable recovery.
- The file itself cannot be read in isolation. It depends on the SYSTEM and SECURITY registry hives, since the Boot Key (syskey) from these hives is required to decrypt sensitive fields such as password hashes.
- The size of the file depends on the environment. In small organizations, it may only be a few megabytes, while in large enterprises with thousands of accounts and objects, the database can grow into gigabytes.
How NTDS.dit extraction works
This section outlines the step-by-step execution of the NTDS.dit extraction attack, discusses common attack methods, and explains why NTDS.dit password extraction is a primary goal for attackers seeking domain-wide credentials for persistent, high-impact access across the enterprise.
Step-by-step execution
An NTDS.dit extraction attack unfolds in a series of steps. The attack starts with an initial breach, steals the NTDS.dit file (and SYSTEM hive) by making a copy of these from a domain controller, recovers and decrypts password hashes, cracks or reuses those credentials, and finally achieves domain-wide compromise.
- Initial access: Attackers gain initial access to the target network through methods such as phishing campaigns, exploiting software vulnerabilities, using stolen credentials, and leveraging misconfigurations.
- Privilege acquisition: The attacker then obtains high privileges (Domain Admin or local SYSTEM on a domain controller).
- Domain controller access: With elevated rights, the actor gains access to the domain controller’s file system and registry hives, either on a live host, a snapshot, or a backup image.
- NTDS.dit acquisition: The adversary obtains a copy of the NTDS.dit file (or a logical extract of its contents) via snapshot/backup mechanisms, administrative utilities, or by stealing a virtual disk image. The goal is an offline copy that can be analyzed outside the live DC environment.
- SYSTEM hive retrieval: The attacker also acquires the SYSTEM (and sometimes SECURITY) registry hive because they contain the boot key material needed to interpret or decrypt certain protected fields in NTDS.dit.
- Off-host analysis / decryption: Using the copied files and key material, the adversary parses the database and extracts password hashes and credential blobs. Tools like
secretsdump.py(Impacket) andDSInternalsare commonly used for this purpose. The SYSTEM hive contains the Boot Key (SYSKEY), which attackers use to decrypt the Password Encryption Key (PEK) stored in NTDS.dit. This PEK is then used to decrypt NTLM hashes, Kerberos keys, and other protected credential data from the database. - Credential exploitation: After extracting password hashes, attackers either crack the NTLM hashes using tools like Hashcat or John the Ripper to obtain plaintext passwords, or leverage Pass-the-Hash (PtH) techniques to authenticate directly using the hashes without cracking them, enabling faster lateral movement across the network.
- Post-exploitation goals: With credentials, attackers move laterally within the AD environment, access sensitive resources, persist, and may pivot to cloud identities and external systems.
Attack methods
Attackers use sneaky and legitimate-seeming techniques to obtain NTDS.dit and related directory data. They choose a method that best balances stealth, ease, and impact for the target environment.
Method | Description |
|---|---|
|
Direct offline copy (risky) |
Adversaries can stop AD services and copy the database directly. This method yields a clean copy but it is disruptive and easily detected. Adversaries rarely choose this unless they control the DC. |
|
Volume Shadow Copy Service (VSS) / snapshot abuse |
Threat actors leverage snapshot and backup mechanisms (such as vssadmin, ntdsutil) to obtain a copy of locked files like NTDS.dit and the SYSTEM hive without stopping services. Alternatively, attackers with sufficient privileges may use DCSync to extract credentials, bypassing the need for file exfiltration. These methods are less disruptive and evade naive detection. |
|
PowerShell and administrative tools abuse |
Attackers turn legitimate admin tools, such as PowerShell modules (including PowerSploit’s |
|
Virtualization compromise / disk image theft |
Attackers can steal a VMDK/VHD or snapshot of a DC from hypervisors or backup systems, so they can analyze an offline image outside the production environment. |
|
Backup compromise |
Backups contain AD artifacts like NTDS.dit and registry hives. If attackers are able to access these backups, they have a low-risk way to pull a copy of the database. |
Persistence
Extracted NTDS.dit data works for attackers long after the breach, allowing them to reuse credentials, forge tickets, and maintain access across the environment.
- Longevity of value: Extracted NTDS.dit material remains useful long after an initial compromise. Attackers can crack passwords offline and execute attacks such as pass-the-hash at any given time.
- Backups as time capsules: Old backups may include credentials and the krbtgt keys for lengthy periods. As many organizations do not frequently rotate the key, even stale copies can facilitate long-term compromise.
- Domain-wide consequences: With hashes for high-privilege accounts or the krbtgt account, attackers can forge Kerberos tickets, impersonate accounts, and maintain persistent, domain-wide access.
- Cross-environment pivoting: Credentials stolen from AD can work outside the corporate network (for SSO, cloud federations, and VPNs), letting attackers jump to other systems and steal data.
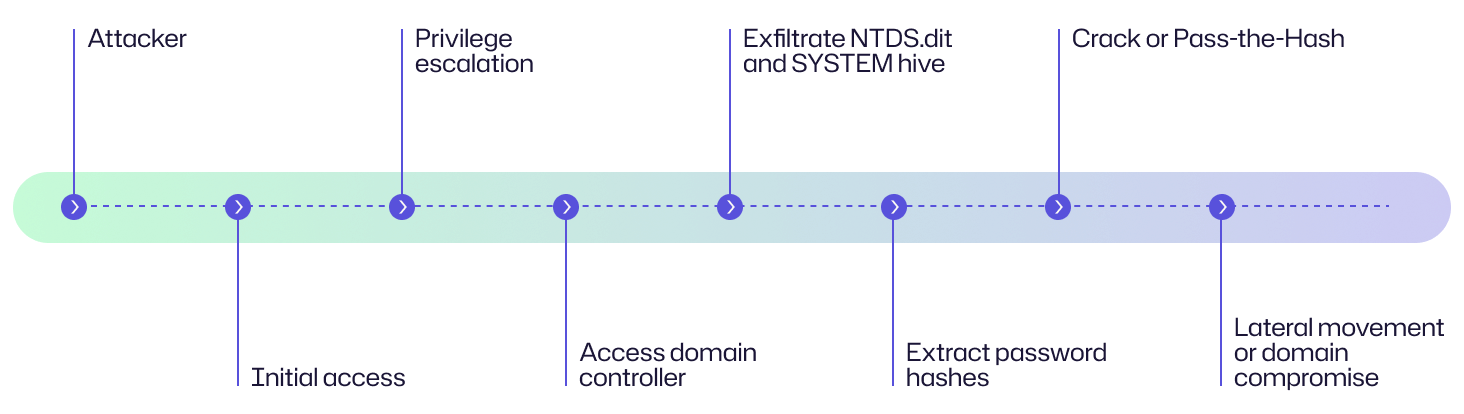
Attack flow diagram
To help you understand the NTDS.dit extraction attack, here is a flow diagram explaining the chain of events, accompanied by an example from an organization’s perspective.
At a manufacturing facility, an employee clicks a malicious link and the attacker gains initial access to a user workstation. The attacker escalates privileges and laterally moves until they obtain admin rights on a server that can reach a domain controller. Using the server’s backup access, they quietly copy a Volume Shadow snapshot containing NTDS.dit and the SYSTEM hive. Offsite, they extract password hashes and recover credentials for several high-privilege accounts. With those credentials, they forge access to cloud-linked services and move laterally across the corporate network, exfiltrating sensitive intellectual property.
Examples of NTDS.dit extraction
Real-world incidents show that NTDS.dit dump is a high-impact path to long-term persistence, lateral movement, and data theft.
Case | Impact |
|---|---|
|
Akira ransomware (2024) |
Akira ransomware emerged in March 2023 and by January 2024, it had impacted over 250 organizations across North America, Europe, and Australia, claiming approximately $42 million in ransomware proceeds. The actors frequently attempted to copy the SYSTEM registry hive and NTDS.dit file from domain controllers to obtain user accounts and their password hashes. In a notable 2024 incident, Akira ransomware operators targeted the AD database by shutting down the domain controller's virtual machine, copying the VMDK files to another VM, and extracting the NTDS.dit and SYSTEM hive files. Using stolen credentials, they escalated privileges to a domain administrator and compromised additional systems in a matter of hours. |
|
Mustang Panda (2023) |
Mustang Panda (also known as Stately Taurus) is a Chinese APT group that conducted a multi-year cyber-espionage campaign from at least Q2 2021 to Q3 2023 targeting a Southeast Asian government. Threat actors used the vssadmin tool to create a volume shadow copy of the C:\ drive on the DC, then retrieved the NTDS.dit file from the shadow copy along with the SYSTEM file containing the boot key to decrypt NTDS.dit. The attackers gathered and exfiltrated sensitive documents from compromised networks. They focused on maintaining long-term access for continuous intelligence gathering from targeted government officials and employees. |
|
Volt Typhoon (2023) |
Volt Typhoon, a Chinese state-sponsored threat group, conducted a cyber-espionage campaign targeting critical infrastructure organizations across the United States from at least 2021 through 2023, with evidence indicating that they maintained persistent access within some victim environments for at least five years. The campaign focused on the communications, energy, transportation, and water and wastewater sectors in the United States and US territories including Guam. To achieve full domain compromise, Volt Typhoon actors moved laterally to domain controllers, then executed the Windows-native vssadmin command to create volume shadow copies. They copied NTDS.dit and the SYSTEM registry hive from the volume shadow copies, then exfiltrated these files to crack passwords offline. |
|
RA World (2024) |
RA World, formerly known as RA Group, impacted organizations in the manufacturing and healthcare sectors in the United States, Europe, and Southeast Asia from March 2024 onwards. After an initial compromise, RA World used the Impacket tool to execute remote commands that copied the NTDS database from domain controllers and exported the SYSTEM and SAM hives. These files enabled RA World to crack credentials offline and gain domain administrator privileges, supporting their multi-extortion ransomware operations where they stole sensitive data, encrypted systems, and threatened to publish stolen information on their leak site if ransom demands were not met. |
Consequences of NTDS.dit extraction
The NTDS.dit file acts as the key to an organization’s authentication system. With every password hash and Kerberos ticket at an attacker’s disposal, the effects can cascade across finance, operations, reputation, and regulatory exposure.
Impact area | Description |
|---|---|
|
Financial |
NTDS.dit extraction can lead to significant financial losses through both direct and indirect costs. Organizations face immediate expenses from incident response, forensic investigation, and system restore. They also incur indirect costs from potential fraud and extended downtime that disrupts business operations. If ransomware is involved, ransom payments, data theft, or credential resale can further amplify losses. |
|
Operational |
A compromised Active Directory environment with stolen credentials and password hashes can cripple core authentication and access processes and other domain controller operations, disrupting user logins, group policies, and domain-joined applications. This operational breakdown can halt automated services, critical workflows, and even entire business units that rely on identity-based access. |
|
Reputational |
Credentials exposure and unauthorized access to sensitive systems can severely damage an organization’s repute. Customers, partners, and stakeholders may lose confidence in the company’s ability to safeguard their data, leading to lost contracts, negative publicity, and long-term brand erosion. |
|
Legal/regulatory |
The theft of Active Directory credential data can trigger data breach laws like GDPR, HIPAA, or other regional privacy regulations. When this happens, organizations may be required to inform the authorities and affected users within a specific timeframe. Beyond potential fines or lawsuits, they can also face reputational fallout and tighter scrutiny from regulators. |
Common targets of NTDS.dit extraction: Who is at risk?
Any organization running Active Directory is a potential target for an NTDS.dit extraction attack, and that’s almost everyone. Let’s look at who is most at risk.
Enterprises with Active Directory
Nearly every large enterprise relies on Active Directory to manage users, devices, and access. Indeed, 99% of the Fortune 500 companies do. Because AD is so deeply integrated into daily operations, attackers know that compromising it means instant, broad control. Once they get their hands on NTDS.dit, they can move laterally across the entire network with minimal resistance.
Organizations with hybrid AD and Entra ID setups
Hybrid environments, where on-prem AD syncs with Microsoft Entra ID, widen the attack surface. By compromising the on-prem NTDS.dit file, attackers do not just get local access; they can pivot into your cloud resources. Password hash synchronization, federated authentication, and pass-through authentication all create pathways. By the time suspicious cloud behavior surfaces, attackers have already cracked passwords, escalated privileges, and established persistence in both environments.
High-value sectors
The healthcare, government, finance, defense, and education sectors hold vast amounts of sensitive data (patient records, financial information, intellectual property, and classified assets), making them prime espionage and ransomware targets. Attackers also know that downtime in these industries is costly, which gives them more power to force victims into paying.
Specific targets: domain controllers, backup repositories, and virtualized DCs
Domain controllers are always the main prize, but attackers also look for indirect ways to grab NTDS.dit. Backups, system snapshots, and virtualized domain controller images (like VMDKs or Hyper-V files) contain exact copies of AD databases. If those backups are not encrypted or isolated, they become the easiest path to a full credential theft.
Risk assessment
To assess the risk of an NTDS.dit extraction attack, consider three key factors: the potential impact if attackers obtain your Active Directory database, how difficult it is for them to carry out the extraction, and how likely such an attempt is in your environment. Together, these factors highlight the importance of protecting and monitoring domain controllers and AD artifacts for enterprise security.
Risk factor | Level |
|---|---|
|
Potential damage |
Critical |
|
Ease of execution |
Medium |
|
Likelihood |
Medium–High |
How to prevent NTDS.dit extraction
Protecting the Active Directory database calls for a layered defense that limits privilege exposure, enforces strong authentication, and continuously monitors for suspicious behavior. The following measures can significantly reduce the risk of NTDS.dit extraction.
Limit privileged access
Attackers can only extract NTDS.dit if they gain administrative or SYSTEM-level rights, so minimizing privilege exposure is critical.
- Limit membership in Domain Admins, Enterprise Admins, and other high-privilege groups to essential personnel only.
- Apply a tiered administration model (Tier 0–2) to isolate critical accounts and servers.
These measures prevent lateral movement and ensure that compromise of a lower tier (like a workstation) does not lead directly to a domain controller.
Enforce strong authentication
Weak or reused credentials remain one of the easiest entry points for adversaries. You should:
- Enforce multi-factor authentication (MFA) for all privileged accounts and service administrators to block credential replay and brute-force attacks.
- Disable or block legacy authentication protocols such as NTLM and basic authentication that attackers can abuse to bypass security controls.
Harden domain controllers
The best defense against NTDS.dit extraction starts with making domain controllers as difficult to compromise as possible. Consider the following:
- Run domain controllers on dedicated, secured servers isolated in their own network segment, no file shares, no web services, nothing internet-facing.
- Apply regular OS and Active Directory patches to close known vulnerabilities.
- Disable every unnecessary service and port, starting with Print Spooler, which has been exploited repeatedly to gain SYSTEM access. Use strict firewall rules that only allow essential AD traffic. Every extra service, open port, and administrative share on a domain controller can expose NTDS.dit to unauthorized access.
Monitor for suspicious activity
Early detection can make the difference between an intrusion and a full domain compromise.
- Enable command-line logging and audit for tools like ntdsutil.exe, vssadmin.exe, wmic.exe, and other snapshot utilities that are often used to access or copy NTDS.dit.
- Monitor Windows Event IDs such as 325, 327, and 4104, which can reveal suspicious attempts to access or copy NTDS.dit.
- Event ID 325: Logged by ESENT when a database like ntds.dit is attached or accessed. It may indicate unauthorized AD database access.
- Event ID 327: ESENT event showing database detach or shutdown. It is useful for spotting NTDS.dit copy or dump activity.
- Event ID 4104: PowerShell script block logging event. It reveals the execution of suspicious scripts or commands (such as ntdsutil, vssadmin) used for NTDS.dit extraction.
- Use EDR and SIEM solutions to detect and alert on unusual file or registry hive access patterns.
Protect backups
Because NTDS.dit and SYSTEM hive files are often included in backups, protecting those backups is just as important as protecting the domain controller itself.
- Always encrypt AD backups, restrict access to backup storage locations, and ensure that your backup infrastructure is hardened against tampering.
- Regularly rotate the krbtgt account password to invalidate any stolen Kerberos tickets that could be used for persistence.
Adopt security frameworks
Frameworks like zero trust and Microsoft’s Enterprise Access Model provide structured ways to strengthen AD security.
- Implement zero trust principles to verify every access request, even from inside the network.
- Use Microsoft LAPS (Local Administrator Password Solution) or similar tools to ensure that local administrator passwords are unique and rotated automatically. This can limit lateral movement if one host is compromised.
Regular auditing and testing
Even with controls in place, continuous validation is essential. You must:
- Conduct regular Active Directory audits to identify unauthorized privilege escalations, group membership changes, and misconfigurations.
- Schedule penetration tests or red team exercises focused on AD and credential theft scenarios to verify defenses and uncover any detection gaps.
How Netwrix can help
Netwrix offers several products and capabilities that can help mitigate or detect the conditions leading to NTDS.dit extraction attacks. It focuses on detection and response, audit trail, access governance, risk visibility, and alerting, filling gaps that traditional tools may miss. The following table shows how Netwrix offerings can support your defense against NTDS.dit theft:
Netwrix product / solution | How it helps prevent or detect NTDS.dit extraction |
|---|---|
|
This product provides audit logging of configuration changes, AD object changes, and user activity across Active Directory, Windows Server, and other IT systems. It can detect abnormal changes to domain controllers, group memberships, and unauthorized access to critical files and registry. It can also detect unauthorized access attempts to domain controllers and flag Volume Shadow Copy service activity (commonly used in NTDS.dit extraction). |
|
|
This product delivers just-in-time privileged access, manages and enforces privileged account usage, and eliminates standing privileged accounts. It restricts who can initiate privileged sessions on domain controllers and enforces approval workflows for DC access. By limiting which accounts can act on DCs (and for how long), it directly controls the type of access that an attacker needs to extract NTDS.dit. |
|
|
This product assesses the risk of access permissions, helps identify over-privileged accounts, and risky access paths. It is useful for tightening who can access what, and reducing the number of accounts that could reach a DC. |
|
|
This product automates and controls directory changes (users, groups, permissions). It can help enforce best practices around group membership and prevent privilege creep, so that fewer accounts are in high-risk roles. |
|
|
The ITDR solution monitors identity paths, escalations, and unusual identity-based behavior in real-time. Abnormal credential or AD abuse patterns may light up here, especially when combined with other detection controls. The solution blocks risky changes and provides automated response actions for both on-premises and hybrid Active Directory environments. |
Protect sensitive Active Directory data and detect unauthorized access with Netwrix Identity Threat Detection & Response (ITDR). Download free trial.
Detection, mitigation, and response strategies
To defend against NTDS.dit extraction and related Active Directory compromise attempts, organizations need a comprehensive strategy that covers detection, mitigation, and response. Here are some practical measures.
Detection
By detecting suspicious activity targeting the NTDS.dit file early, security teams can prevent full domain compromise. Early detection measures include:
- Monitor for suspicious tool usage: Track unusual executions of ntdsutil.exe, esentutl.exe, vssadmin.exe, and backup utilities. Attackers tend to abuse these tools to create or copy AD database snapshots.
- Review shadow copy creation events: Look for Event IDs 7036 (service start/stop) and 8222 (VSS shadow copy creation), especially when these are initiated outside maintenance windows or by non-administrative users.
- Track NTDS.dit file access attempts: Configure auditing on domain controllers to detect direct reads, copies, or movement of the NTDS.dit file and SYSTEM registry hive.
- Detect replication abuse (DCSync): Monitor directory replication requests from non-DC systems. Alerts should trigger if DRSUAPI or DS replication APIs are invoked by unauthorized hosts or accounts.
- Correlate unusual admin behavior: Investigate anomalies such as sudden privilege escalations, new shadow copy tasks, or domain replication from unexpected endpoints.
Mitigation
Mitigation controls reduce the likelihood of attackers obtaining or exploiting domain controller data. Key steps include:
- Enforce an administrative tiering model: Implement Microsoft’s Tier 0/1/2 structure to isolate high-privilege accounts (such as DC admins) from lower-trust systems. This prevents a compromise in lower tiers from reaching higher ones.
- Use just-in-time (JIT) privileged access: Provide temporary elevated rights to administrators or specific accounts only when needed, through solutions like Netwrix Privilege Secure. This minimizes standing privileges, limits exposure time for high-level access, and reduces the risk of credential theft or misuse.
- Regularly rotate the krbtgt password twice: Rotate the krbtgt account password two consecutive times to invalidate any forged or cached Kerberos tickets, such as those created in Golden Ticket attacks. This ensures that previously issued tickets become unusable.
- Require multi-factor authentication (MFA): Enforce MFA for all privileged and administrative logons, including RDP, PowerShell remoting, and AD management consoles.
- Secure backups: Encrypt AD backups and restrict access to them. This prevents attackers from retrieving NTDS.dit through backup data.
- Disable legacy authentication methods: Turn off outdated protocols such as NTLM, LM, or Basic Authentication where possible to reduce credential theft vectors. Instead, enforce Kerberos or modern authentication (OAuth, SAML, or certificate-based) mechanisms.
- Apply network segmentation: Isolate domain controllers on a dedicated, restricted network segment. Only authorized administrative jump servers or Tier 0 systems should have network access to DCs.
Response
If an NTDS.dit extraction or domain compromise is detected, take swift and structured response actions.
- Isolate compromised domain controllers: Immediately disconnect affected systems from the network to contain the breach and prevent further lateral movement or data exfiltration. Disable their replication connections and block communication with other DCs.
- Rotate privileged credentials: Reset all administrative, service, and shared accounts, starting with Tier 0 identities such as Domain Admins, Enterprise Admins, and service accounts linked to domain controllers. After containment, consider rotating the krbtgt key again to fully invalidate any lingering Kerberos tickets or unauthorized tokens.
- Rebuild compromised infrastructure: If persistence mechanisms or DC tampering are confirmed, rebuild the affected domain controllers from clean, trusted sources rather than restoring from potentially infected backups. After rebuilding, reapply security baselines and patch all systems before bringing them back online.
- Conduct forensic analysis: Examine shadow copies, backup data, event logs, and memory dumps to trace attacker activity, identify persistence mechanisms, and detect any data exfiltration attempts. Focus on analyzing NTDS.dit access, replication events, and PowerShell or administrative tool usage for signs of credential theft. Correlate findings with threat intelligence.
- Notify regulators if a data breach occurred: If sensitive credentials or user data were exposed, follow your organization’s incident response and legal notification procedures. Some regulations, such as the GDPR (72 hours) and HIPAA (60 days), require reporting a confirmed breach within specific timeframes. Notify relevant regulatory authorities, affected customers, and partners as required.
Industry-specific impact
Cyberattacks targeting NTDS in Windows and other identity systems can have devastating consequences across industries. The impact varies by sector but commonly includes regulatory violations, financial losses, and long-term reputational damage.
Industry | Impact |
|---|---|
|
Healthcare |
A breach in healthcare environments violates HIPAA compliance, exposes Protected Health Information (PHI), and enables attackers to steal, manipulate, or encrypt patient data through ransomware. Attackers may also use compromised AD credentials to disrupt hospital systems, delay patient care, and access medical devices, potentially endangering lives. |
|
Finance |
Financial institutions face PCI-DSS violations, unauthorized fund transfers, and theft of customer banking credentials or trading information. Attackers can escalate privileges across payment systems, leading to large-scale fraud, identity theft, and regulatory penalties. Extended downtime or data exposure can also severely damage credibility and customer trust. |
|
Government |
In the public sector, AD compromises can lead to espionage, data theft, and sabotage of critical infrastructure. Attackers may gain persistent access to sensitive records, disrupt essential services, and even manipulate authentication systems across departments. Overall, such breaches can pose serious national security threats. |
Attack evolution and future trends
Defenders now face a far more complex NTDS.dit threat landscape. Attacks that once required local access and specialized tools can now happen through cloud and hybrid environments. Modern attackers embed NTDS.dit extraction into ransomware playbooks and use legitimate Windows utilities to hide their activity, making these attacks faster, stealthier, and harder to detect.
Key statistics and infographics
The following numbers clearly show how central Active Directory remains in modern attacks and why NTDS.dit extraction continues to be such a high-impact technique.
- Verizon’s DBIR (2024) shows the use of stolen credentials was the initial action in about 24% of breaches overall. In the DBIR 2024 “Basic Web Application Attacks” pattern, stolen credentials accounted for roughly 77% of the hacking actions. This highlights just how valuable AD credential stores are to attackers.
- Microsoft telemetry shows that more than 99.9% of the accounts their systems observed being compromised did not have MFA enabled. This is a striking indicator of how effectively MFA blocks automated and credential-based attacks.
- Coveware’s incident data shows that ransomware incidents involving Active Directory caused an average of about 21 days of business interruption (Coveware Q4 2020 analysis), highlighting how deeply identity compromise disrupts operations and recovery.
Extraction methods bar chart
The following bar graph shows the most common tools used in NTDS.dit extraction attacks, based on documented incidents from 2022 to 2024.
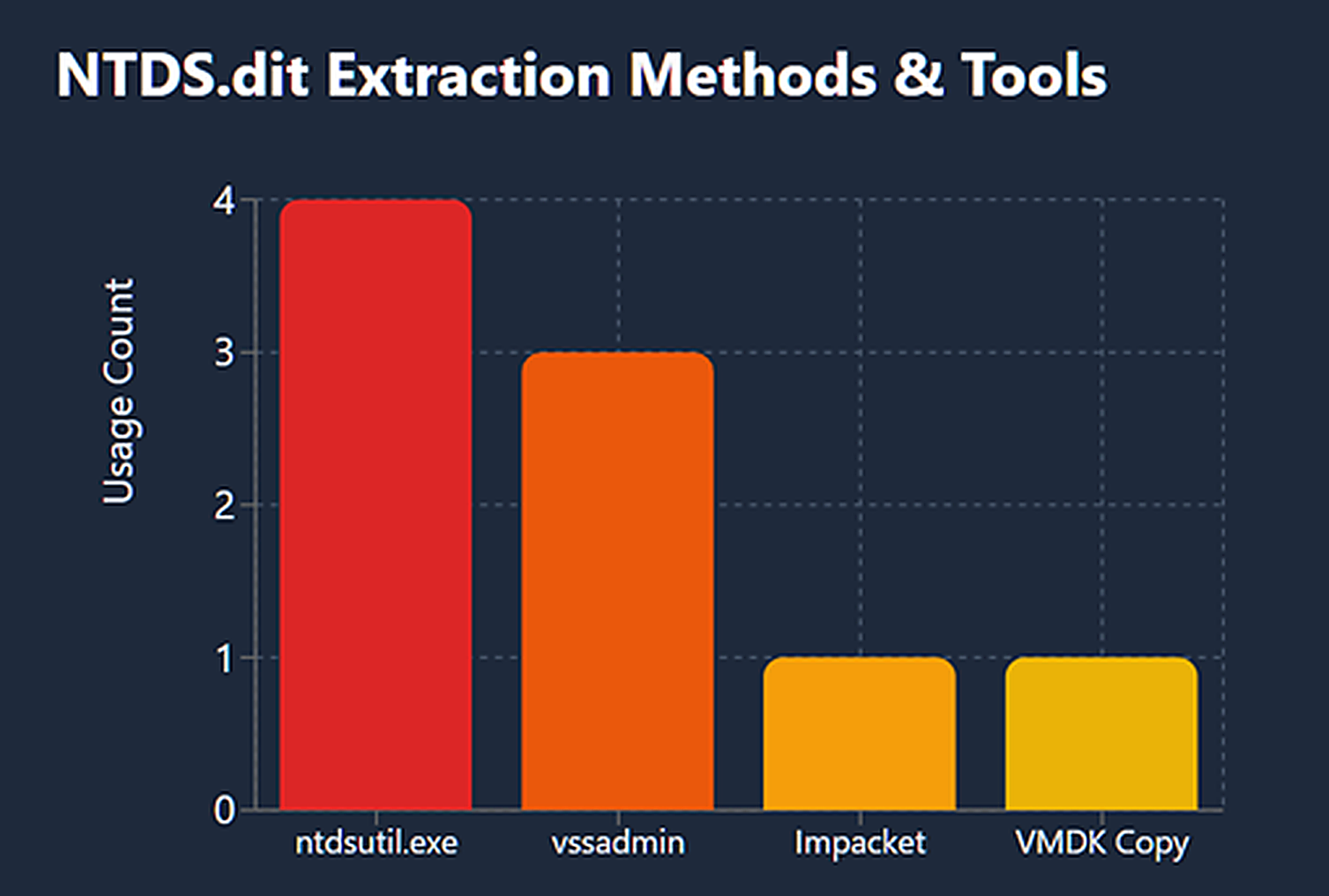
Note that this data is based on publicly documented incidents only. The actual frequency of these methods in the wild is likely much higher.
Final thoughts
The NTDS Active Directory database (NTDS.dit) stores all directory information, including user accounts, passwords, and domain configurations, which makes it a critical component of Windows Server security.
NTDS.dit extraction is a fast, high-impact way for attackers to turn stolen identities into full domain takeover. In today’s hybrid environments, that risk only grows. To protect your identity infrastructure, enforce MFA, lock down and monitor Microsoft Entra Connect and sync ops, detect Living off the Land (LOTL) activity and unusual SYSTEM/NTDS access, and bake AD forensics into your incident-response plans. This will dramatically reduce the odds that a single credential theft becomes a full-blown outage.
FAQs
Share on
View related cybersecurity attacks
Abusing Entra ID Application Permissions – How It Works and Defense Strategies
AdminSDHolder Modification – How It Works and Defense Strategies
AS-REP Roasting Attack - How It Works and Defense Strategies
Hafnium Attack - How It Works and Defense Strategies
DCSync Attacks Explained: Threat to Active Directory Security
gMSA exploitation attacks and Golden gMSA attacks explained
Ultimate guide to Golden SAML attacks
What Is a Golden Ticket Attack? How It Works, Detection and Prevention
DCShadow Attack – How It Works, Real-World Examples & Defense Strategies
ChatGPT Prompt Injection: Understanding Risks, Examples & Prevention
Kerberoasting Attack – How It Works and Defense Strategies
Pass the Hash Attack
Pass-the-Ticket Attack Explained: Risks, Examples & Defense Strategies
Password Spraying Attack
Plaintext Password Extraction Attack
Zerologon Vulnerability Explained: Risks, Exploits and Mitigation
A complete guide to ransomware attacks
Skeleton Key attack: how it works and how to detect it
Lateral Movement: What Is It, How It Works And Preventions
Man-in-the-Middle (MITM) Attacks: What They Are & How to Prevent Them
Why Is PowerShell So Popular for Attackers?
4 Service Account Attacks and How to Protect Against Them
How to Prevent Malware Attacks from Impacting Your Business
What is Credential Stuffing?
Compromising SQL Server with PowerUpSQL
What Are Mousejacking Attacks, and How to Defend Against Them
Stealing Credentials with a Security Support Provider (SSP)
Rainbow Table Attacks: How They Work and How to Defend Against Them
LDAP Reconnaissance
Bypassing MFA with the Pass-the-Cookie Attack
Silver Ticket Attack
